You’ve Been Hit By Ransomware. Now What?
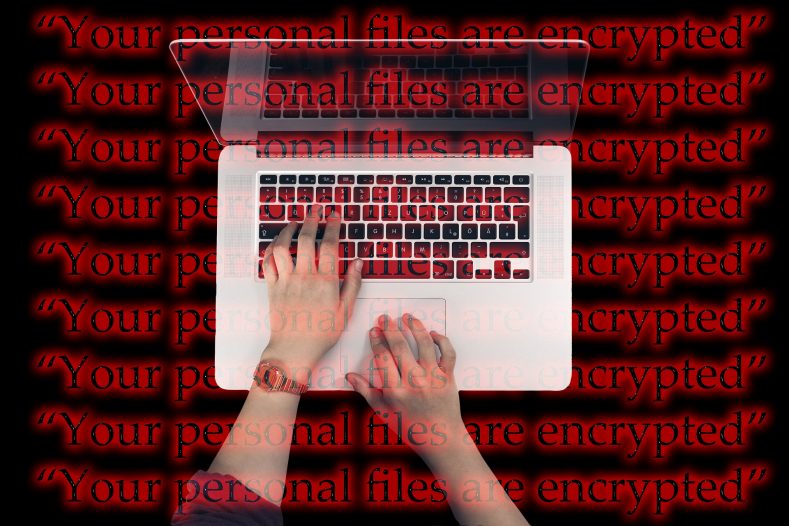
“ALL YOUR FILES HAVE BEEN ENCRYPTED”
You see that line flashing on your laptop or desktop and suddenly your adrenaline level shoots up with hundreds of questions already hitting your mind…
How Do I Remove that Message?
Why Can’t I Access My System?
Will I Lose All My Work?
Whom Should I Approach For Help?
Well, instead of entering the panic mode and instantly jumping on to Google for a quick help, it’s better to keep your calm and simply follow these simple steps:
Disconnect From All Connected Systems – In case your system is connected to a Wi-Fi network or external drive, then the very first thing you can do is to disconnect your infected system from all of these. This may save the ransomware from spreading to other connected networks and devices since most cyberattacks spread from connected systems.
Capture A Pic – Use a camera or smartphone to click a pic of the ransom note visible on your screen, as you may need it for making a police complaint later. Capture a screenshot of the ransomware screen if your system allows you to do so.
Do A Quick Research – Once you have taken the few initial steps to isolate your infected system from other connected systems and collected some proofs, you can then invest some time in doing a quick research. Most often the ransom notes are transparent and contain the name of the ransomware along with an email address. However, at times there may be no name for the ransomware and there are huge chances that it may be a total bluff. At such times, it can prove really handy to do a little research on the name of the ransomware, to confirm its authenticity.
Contact The Law Enforcement – Since, ransomware hacking is a big time crime, you can and should contact your local law enforcement agency to report the incidence. The best people to approach however, are the specialized cybercrime cells and cyber police stations available in most states, for handling cybercrime issues. These cells may be available in the form of Serious Fraud Investigation Office, Economic Offence Wing or State CID Department.
Reboot To Safety – Before you try rebooting your system, be absolutely determined about not paying the ransom amount under the temptation of recovering your files. Once you have made up your mind, reboot your system into “Safe Mode” simply by holding the S key on your keyboard and pressing the power button at the same time.
Try Recovering Deleted Files – The way most of the encrypting ransomware work, is they make copies of your files, encrypt these copies and then simply delete the original files. At times, there are major chances of recovering the original deleted files using free or paid file recovery tools. Who knows, you may just be lucky enough to get back your files!!
Look For Decryption Tools – Just in case you have an idea about the ransomware strain, simply check out the list of decryption tools available on web. Quick Heal is quick to assist at such critical times by releasing the decryption key publicly on our website or blog, as soon as our security lab professionals are through with decryption. We have done this in the past with decryption tools for CrySiS/XTBL Ransomware, TeslaCrypt Ransomware and more.
So, regardless of the frustration we may go through as a result of these cyber-attacks, the truth is that these ransomware and malware are here to stay. Thus, instead of panicking about them, it’s better to fight back and simply update our security systems, to be well prepared for any future attacks.
No Comments, Be The First!