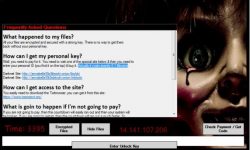
Decryption Tool for TeslaCrypt Ransomware Infection

If our readers can recall, in an earliest post we had discussed TeslaCrypt – what it is and what it does. This post has some important information related to recent findings from our Labs. Read on to know more.
First, a brief flashback!
Current Situation
Although downright evil and malicious, malware authors are ambitious. If you thought that the TeslaCrypt authors stopped working after creating the first version of this malware, then you would be wrong. The latest version of this malware, reportedly released in November 2015, is known as ‘v8’ or ‘v2.2.0’. While it is not certain how many variants of this malware have been spawned since its inception, the latest version clearly states that the hackers have been keeping themselves busy.
The Quick Heal Threat Research Labs was recently reported about 60+ cases of TeslaCrypt infection. Apparently and fortunately, the encryption tool used by this particular variant is weak and can be broken to reveal the key that is required for decrypting the locked data.
Below is a link to a free tool that can be used by those who fell victim to the latest TeslaCrypt infection and their files were encrypted.
https://github.com/Googulator/TeslaCrack
Note:
• TeslaCrypt 2.0 infection can be recognized from the extension “.vvv” added to the names of the encrypted files.
• The recovery process takes a good amount of time so one needs to be patient; also, this tool does not guarantee the recovery of files in all cases.
A word of advice
The steps described for using this tool are not meant for novice users. So, if you are not sure about them, consider seeking assistance from a computer technician or a friendly neighbor who happens to be a computer geek.
To conclude, here are some safety measures to stay away from ransomware attacks:
- Never download attachments or click on links in emails received from unwanted or unexpected sources, even if the source looks familiar.
- Don’t respond to pop-up ads or alerts while visiting unfamiliar websites.
- Apply all necessary security updates to your OS, software, and Internet browsers. Always keep automatic updates ON.
- Have a security software installed in your PC that efficiently blocks spam and malicious emails, and automatically restricts access to malicious websites.
And, the most crucial step – while doing this will not save you from a ransomware infection, but will certainly help you recover. Take regular data backups. Ransomware goes after your data, and then threatens you to pay up in exchange for the data. So, if you have a backup, then you are guarded against extortion – which is, in fact, the most important part here.
We will keep you posted if we come across anymore important findings about TeslaCrypt or any of its nasty family members. Stay tuned to our blog, and stay safe!

23 Comments
I had written about this to the Quick Heal support team a few days ago.
Unfortunately there was no reply.
I had to format my PC to get out of the situation.
Hopefully this article of yours would help, if someone in my contacts faces the same problem.
Hi Jayant,
Thanks for writing in. We are regretful that we could not come to your aid on time. We have shared your feedback with our team.
Regards,
Team QuickHeal,
Thanks my PC is safe. But copying docs from PC into a Folder in my Pen Drive for printing outside, all docs in that folder got corrupted due infection. Can neither open nor delete them. Advised 2 format PenDrive.
Now most UNUSUAL your QuickHeal on my PC as well at printing place does NOT DETECT the infection; as next time printing fm another folder with same vendor another 3-4 docs got corrupted nor able to delete.
Since I am in Pune Camp I can bring over the infected Pen Drive for your investigation. Since it is something Unique and worth investigation.
contact – 9822319994 or 020-26137938
Hi Boman,
Thank you for sharing your experience. We suggest that you contact our technical support team. They will gladly look into this and provide you with instructions on what to do next. You can reach them here – https://www.quickheal.co.in/submitticket.
Regards.
actually this is not a comment
but a question
a few days before i had downloaded a software unintentionally from a site which was unknown to me since i was surfing in the search of an e-book. And in that case it got downloaded by me bcoz i thought that it would help me but it was useless.
Now the problem is that now whenever i open my web browser viz. chrome or mozilla a search engine named “yousearching.com” displays its window and also a green colour border appears surrounding the browser..
What should I do?
pls i need the answer
bcoz i suppose that it slows down my internet’s speed i mean my surfing speed in spite the data transfer rate of the net is having great speed..
Hi Sahil,
Please see this post for instructions on how to reset your browser. That will resolve this issue. If the problem persists, please contact our technical support team. They will gladly assist you with this. You can reach them here – https://www.quickheal.co.in/submitticket.
Regards.
Dear Sir,
My stem infected with cryptolocker, all the xl, word, pdf etc files changed to unknown format. Please help.
Regards,
Kamendra
Hi Kamendra,
May we request you to contact our technical support team. They will help you resolve this issue as soon as possible. You can reach them here – https://www.quickheal.co.in/submitticket.
Regards.
i lost my product key
Hi,
Kindly visit the link given below to retrieve your lost product key:
http://www.quickheal.com/lost
Regards,
Hello
Is there any solution to decrypt the files affected with cryptowall ransomware?
Hi Nageswara,
May we request you to contact our technical support team. They will help you resolve this issue as soon as possible. You can reach them here – https://www.quickheal.co.in/submitticket.
Regards.
very very helpful
I have a subscription of Total Security since 03/11/2011 and validity till 03/01/2019. It works wonderful but from few days It is unable to take updates. I called to Customer care for the same problem. It has been suggested to download the updates. I did the same but the quick heal is not updating self and mannualy. the last database is of 12 dec 2015.
Plz suggest and rectify the problem.
Hi Sharad,
May we request you to contact our technical support team. They will help you resolve this issue as soon as possible. You can reach them here – https://www.quickheal.co.in/submitticket.
Regards.
good
i want to advice you that do not download anything from softanic because it contains malivare
my computer is infected with cryptowall plz help me
Hi Ketan,
Thanks for writing in. Our support engineers would gladly help you with this issue. Please visit https://bit.ly/QHChat to chat with us online. You can also raise a ticket at https://bit.ly/Askus and we will get back to you at the earliest.
Regards,
Dear Sir,
My stem infected with Cerber2, all the video,imeages, xl, word, pdf etc files changed to cerber2 format. Please help.
Regards,
MD ABDUR RAHMAN
Hi Abdur,
Thank you for writing in. Our support engineers would gladly help you with this issue. Please visit https://bit.ly/QHChat to chat with us online. You can also raise a ticket at https://bit.ly/Askus and we will get back to you at the earliest.
Regards,
Hi,
my pc infected by cerber ransomware , my jpegs, pdf & doccuments converted in .B2ed extension , plz help me. i am using quick heal since last year,
Hi Danish,
Thank you for writing in. Please call us on our toll-free no. 1800-121-7377 or visit https://bit.ly/QHChat to chat with us online.
Regards,