Why a Simple Antivirus Isn’t Enough for Small and Midsize Businesses
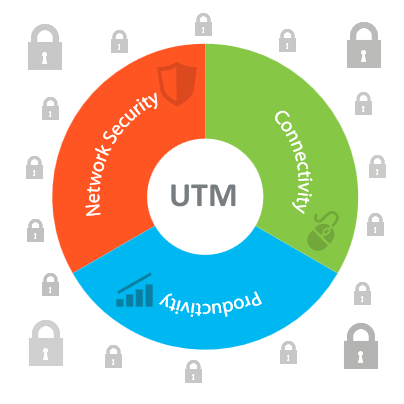
Let’s make peace with the fact that if there is anything that small and midsize businesses are lax about is their IT security. And this what cyber crooks are good at capitalizing at. Instead of burning their energy into taking down big businesses (which general have good IT security defense in place), they aim for small and medium businesses. And given the sophistication of malware at present time, relying only on an antivirus software could be detrimental. It needs to be fortified with what is known as Unified Threat Management. With more and more businesses becoming aware about cyber security, UTM appliances are gaining popularity. These are the key features that UTMs offer and can make a big difference in enterprise IT security:
1. Firewall
To block unauthorized Internet access to the corporate network.
2. Intrusion Detection and Prevention System (IDPS)
Any unpatched application in a corporate network can serve as a doorway for a malware to sneak in and launch a full-fledged attack. This threat can be taken care of by an IDPS. It scrutinizes network traffic, identifies malicious activity in it or in any system, logs its information and blocks it before it breaches the corporate network.
3. Gateway protection
An extra layer of protection that blocks virus, worms, Trojans and other malware right at the circumference of your corporate network.
4. Virtual Private Network (VPN)
In enterprises where employees have to connect to the company’s network while out of office, UTM plays an important role in securing remote access.
5. Bandwidth Manager
Internet bandwidth can be a huge weight on any company’s budget plan. UTMs can allow administrators to allocate bandwidth based on the need of an application or user(s). In this way, the enterprise would only spend on what they need.
6. Web Filtering
UTM can also ensure that the company’s Internet usage policy is adhered to. Administrators can block inappropriate, unnecessary or suspicious websites that can affect employee productivity or risk a malware attack.
7. Automatic Link Failover
UTM also offers the facility to shift network load from an inactive Internet Service Provider (ISP) line to an active ISP. This not only reduces manual shifting of ISP lines but also helps manage any Internet downtime.
Choosing a reliable antivirus solution for your endpoints and fortifying it with a UTM power packed with all these features would transform your enterprise into an iron fort, which even the seasoned of cyber crooks would have a hard time hacking into.
Quick Heal Terminator is a Unified Threat Management Solution designed keeping in mind small and midsize businesses. It is a culmination of all the features discussed in this post. Request a free trial or demo here.
1 Comment
Thank you for this info Rajib sir.
Regards,
Hrushi.