Use Smartphones Only in Emergencies – Government Instructs Ministries to Avoid Loss of Sensitive National Data
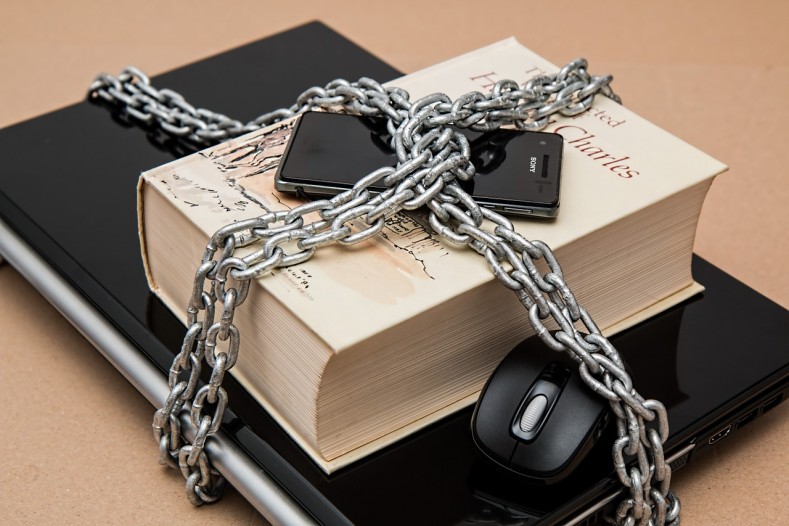
Just like the private sector, the Government has been encouraging its employees to use smartphones for better collaboration within departments. This rapid adoption of smartphones and Internet services in Government organizations might lead to situations where national security could be compromised by a simple data breach. This is a concern which has recently led the Indian Government to instruct its employees and bureaucrats to limit the use of these smart devices to share and discuss work related sensitive information and use smartphones only in times of emergency.
While the Government has implemented progressive initiatives such as ‘Digital India’, it is also taking the necessary measures for addressing the current challenges which may act as a hindrance to its larger vision. The Government is creating awareness amongst its employees on how they can prevent information from getting compromised and safely use smartphones and web based applications at the workplace.
Government agencies can adopt several security tips that will enable them to ensure the integrity of data on their devices such as:
- Using a reliable software solution that is customized for the device
- Avoid keeping sensitive information stored on internal memory or SD card
- Avoid exchange of critical data over messaging apps such as WhatsApp as they can be intercepted
- Never connect Government devices to free or unverified Wi-Fi connections
- Never open any links received from unknown senders over emails or SMS on these devices
- Never download any attachments that are received from unknown senders
- Always verify apps and app publishers even while downloading from the official Google Play store
- Never connect the device to unknown machines for charging or for transferring data and with unknown devices over Bluetooth, screen mirroring or mobile tethering
By adhering to these security tips, Government ministries can ensure the integrity and the security of their data. This security is essential today as even a small breach in one device can open up the entire network and its stored sensitive data to an advanced hacker.
The blog is inspired by an article published in The Times of India dated June 5, 2016.
No Comments, Be The First!