The Top 20 Android Malware – Quick Heal Mobile Threat Report
Since the time Android made its entry into the Smartphone arena, it ruffled quite a few players; even the big ones. At present time, Google Android grips a tight 51.6% of the US market share (source: www.androidcentral.com, report as of August 2013).
The open source nature of Android has made it the most popular mobile platform in the world. But as they say, every Dr. Jekyll has a Mr. Hide with it. The overwhelming popularity of the green droid, and its staggering market share has placed it on a mantlepiece in the house of hackers and cyber criminals. This is easily evident by the fact that 99.9% of new mobile malware that are spewed by hackers, are designed to target Android. And with the ever increasing use of mobile Internet, Android has easily attracted the attention of budding and seasoned malware authors.
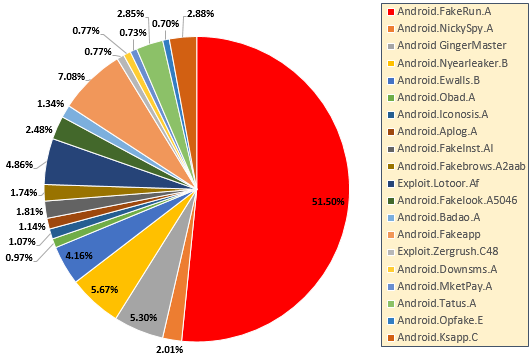
A Quick Roundup of the top 20 Malware as Analyzed by Quick Heal Threat Research and Response Team
1. Android.FakeRun.A
Android FakeRun.A is an Android Trojan horse. It is designed to display ads on the infected device, to earn money for the malware author.
2. Android.NickySpy.A
Android.NickySpy.A is an Android Trojan that steals information from the infected device and sends it to a remote server.
3. Android GingerMaster
Android GingerMaster is an Android Trojan horse. It is typically embedded in a fake version of popular games.
4. Android.Nyearleaker.B
Android.Nyearleaker.B is an Android Trojan horse. This malware comes in the form a live wallpaper application that steals information from the victim’s device.
5. Android.Ewalls.B
Android.Ewalls.B is an Android Trojan. It poses itself as a wallpaper application, and steals information from infected devices.
6. Android.Obad.A
Android.Obad.A is a sophisticated Android malware that gains admin privileges. Once it gains admin rights, it cannot be removed manually from the compromised device.
7. Android.Iconosis.A
Android.Iconosis.A is a Trojan horse designed to steal information from infected Android devices. Once installed, the malware collects the phone number and IMEI number of the compromised device.
8. Android.Aplog.A
Android.Aplog.A is an Android Trojan. It is usually detected as a fake version of legitimate games; Temple Run is one of them.
9. Android.FakeInst.AI
Android.FakeInst.AI is a Trojan. It can allow a hacker to manipulate SMSs and user location in the compromised Android device.
10. Android.Fakebrows.A2aab
Android.Fakebrows.A2aab is an Android Trojan that disguises itself as a legitimate app.
11. Exploit.Lotoor.Af
Exploit.Lotoor.Af is an exploit design to gain root privileges on Android devices. Once installed, the exploit can gain complete privilege of performing any activity on the compromised device.
12. Android.Fakelook.A5046
Android.Fakelook.A5046 is a back door. This malware hides itself from the Application List and collects the identity of the infected device.
13. Android.Badao.A
Android.Badao.A is a Trojan. The malware is designed to manipulate the Short Messaging Service in infected devices.
14. Android.Fakeapp
Android.Fakeapp is a Trojan horse designed for Android devices. The malware displays ads by downloading configuration files without the user’s knowledge.
15. Exploit.Zergrush.C48
Exploit.Zergrush.C48 attacks any vulnerability present in the targeted Android device, to gain root privileges.
16. Android.Downsms.A
Android.Downsms.A is an Android Trojan. Once installed, it sends SMSs to premium-rate numbers, and can write to external storage of the infected device.
17. Android.MketPay.A
Android.MketPay.A is a Trojan. It is usually found repacked in legitimate applications available in many Chinese markets.
18. Android.Tatus.A
Android.Tatus.A keeps a record of applications installed in the device, and sends this data to a remote server. It is a Trojan horse.
19. Android.Opfake.E
Android.Opfake.E is a Trojan horse detected on Android devices. It comes bundled with a legitimate version of the Opera mobile browser.
20. Android.Ksapp.C
Android.Ksapp.C is an Android Trojan. It steals sensitive information and sends the gathered information to a remote server.
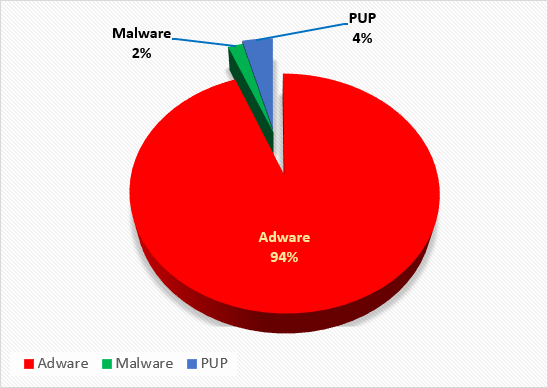
Android Malware Detection by Quick Heal
Total malicious programs detected – 4,31,397
Adware – 94%
Malware – 2%
Potential unwanted programs (PUP) – 4%
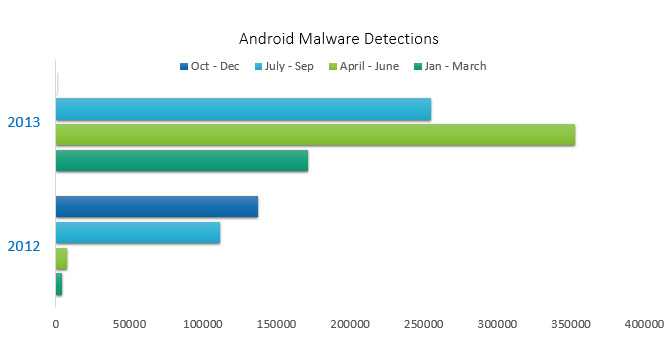
Growth of Android Malware
The following graph gives a brief overview on the growth of Android malware, as observed by Quick Heal Threat Research and Response Team.
Some Quick Facts about Mobile Security
# Most Android apps ask for too much permission even to perform their basic operations.
# Many cyberattacks on mobile phones occur through compromised applications or exploited mobile web browsers.
# Since 2012, malware that target the Android platform has shot up by 600%.
# Reportedly, Jelly Bean seems to have a tighter security compared to the previous versions of the Android OS. However, about 50% of Android devices are running some or the other version of this OS.
# Android malware has already hit the one million mark. This is in stark contrast with PC malware, which took almost a decade to reach this level.
# Smishing is a variant of phishing, where phishers use SMSs to trick their targets. It is an identity theft scheme that attempts to steal sensitive information from the victim. This is done either by tricking the victim into visiting a fake website or call a phone number. In some cases, smishing scams also attempt to drop malware on targeted devices.
# Mobile users are more susceptible to phishing attacks than desktop users. This is because, people readily read text or email messages as soon as they hit the inbox.
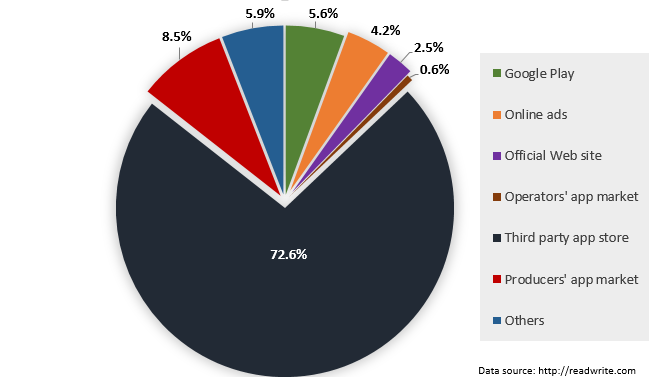
Android Apps Sources
It is always a safe bet to install Android apps from the Google Play Market or from their official sources. But, if you take a look at the following data, you might get a hint behind the explosion of Android malware in the last few years.
According to a study done by AV-Comparatives, third party Android stores play host to around 7,000 dangerous mobile apps.
Time and tide waits for none, neither does technology. It keeps moving on with an ever increasing pace. And where technology goes, cyber crime follows. In this report, we presented to you an analysis of the top 20 malware plaguing the Android platform. And that is the just the tip of the iceberg. Malware authors are hell-bent on developing more sophisticated and nefarious malware. Although there is no silver bullet to deal with this situation, taking the right precautionary measures, using a reliable mobile antivirus solution, and keeping ourselves aware of information security should place us at a safer spot.
In our next blog post, we will discuss how these Android malware work. So, stay tuned!
Blog Post Acknowledgement: Quick Heal Threat Research and Response Team.



3 Comments
Wh.ich is best antivirus for android ?..
AVG
Quick Heal
Avast
Lookout
Dr. Web
Eset
Trustgo
Hello Chaitanya,
Quick Heal Mobile Security (QHMS) protects Android and BlackBerry devices from unseen threats. It also offers call and SMS blocking functionality. Its Anti-theft feature helps you track, lock, and wipe your device in case it is lost or stolen.
Quick Heal Total Security offers all-round protection for Android devices. Apart from having all the basic features of QHMS, it includes Parental Control, cloud backup, and even network monitoring. For more information on both these products, follow:
https://www.quickheal.com/in/en/qhmbs
https://www.quickheal.com/in/en/qhmtsa
Regards,
Really nice info Rajib sir.
Thanks & Regards,
Hrushi.