Some Quick Tips to Keep your Endpoint Data Safe
Corporate cyber attacks have become a common parlance in the world of IT Security. A recent study done by RSA revealed the extent of loss incurred by firms of different nations hit by phishing attacks. The US had to gulp down a loss of $882 million, followed by Germany ($294 million), the UK ($133 million), and India ($53 million). The growing number of such incidents only cements the fact that hacking is no longer limited to some winter holidays’ recreational prank by budding computer geeks. It has rather taken the form of a cash vending machine for cyber criminals.
So, with all such cyber hounds behind to get a bite of your data, your network and money, it is only logical that you fortify your walls and place a sentry at every corner of your fort. We have laid out some basic measures that any small, medium and large enterprise can take to secure their endpoint data.
1. If your employees are utilizing mobile devices to access corporate information, it is a must to mandate PIN or password protection for them.
2. Deploying a Mobile Device Management system is also a wise step to take towards securing your corporate security. With such a system in place, corporate mobile devices can be managed with ease. The admin can update devices’ security settings, monitor apps getting installed on the devices, wipe off data from lost or stolen devices, and so on.
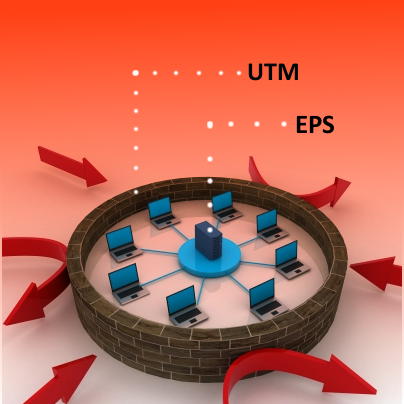
3. You can fortify your corporate network wall by deploying a gateway security solution; in other words, a unified threat management system. From shielding your enterprise from spam, phishing attacks, and other malware attacks, it can also be used to control and manage Internet traffic and usage.
4. When we are speaking of securing endpoint data, we cannot shadow the importance of having a dedicated endpoint security solution. After UTM, this should be the second layer of security your enterprise must have. It can be used to deny system access to unauthorized external drives, scan computers in a network from a central location, allowing or denying computers from executing in the network, scanning your end-user inboxes for spam, phishing attacks and unsolicited e-mail messages, and so on.
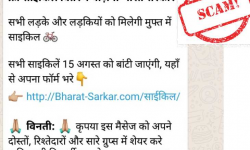
5. Your corporate security is only complete when your users know about the dangers lurking in the wild. Even one of your staff falling prey to a phishing attack can put the entire organization’s data security at stake. You can start by educating them about the importance of creating stronger passwords, not sharing login information, logging off from their computers when not in use, and exercising caution against unknown websites and email messages.
You can also go through this post that talks about the best practices for enterprise IT security.
Quick Heal’s Unified Threat Management system and End Point Security solution offer a multidirectional approach to corporate security, coupled with technological and benefits as well. Request a free demo or trial of these products here.
No Comments, Be The First!