Evolution of Android Malware – Quick Heal Threat Report Q3 2015
We recently reported the notable Windows malware stats and findings from the Quick Heal Quarterly Threat Report Q3, 2015. In this post we will be sharing some insights and interesting findings from the Android section of this report. As per latest data by IDC, there were close to 350 million active smartphones all around the world in Q2 2015, and around 80% of them ran on Android. That leaves about 280 million open-sourced Android devices (or 3.5% of the world’s total population) open to malware attacks, fake apps, Malvertising, phishing scams and more. In Q3, 2015 the number of files detected by the Quick Heal Threat Research Labs over the Android platform and the nature of malicious files detected has thrown up some surprises, but a few shocks. Here, you can view the detailed Quick Heal Threat Report for Q3, 2015.
Android Malware Samples Received by Quick Heal
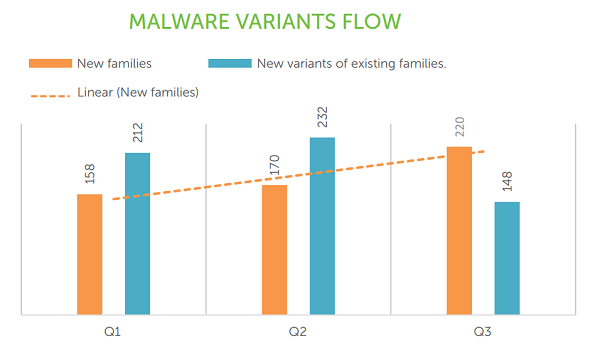
Detection figures of Android samples have exceeded the 1.2 million cumulative mark in the months of July, August and September 2015. In this time period, 220 new families of Android malware have been discovered, and 148 variants of existing families have also been detected. From the graph below, it can also be seen that 500 new Android malware families have been discovered so far in 2015, and over 600 new variants of existing families have also been found.
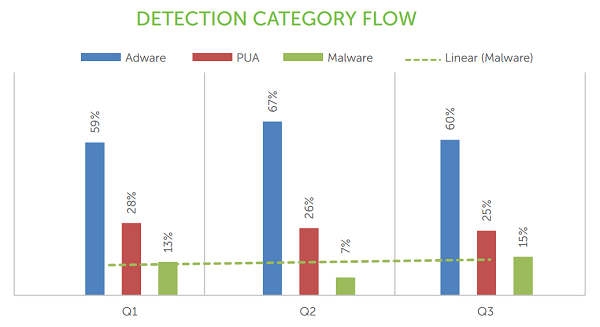
When the Android samples received were broken down further into their categories, the key observation was that Adware constituted two-thirds of all samples received. The details with regards to these can be seen below.
Top 10 Android Malware
Out of all the Android samples received, the most common one was Android.Airpush.G – coming in at 30% of all Android samples. This is an Adware that aggressively pushes ads to the notification bar of compromised devices and adds shortcuts to the homescreen as well. It also modifies device bookmarks and collects and sends various information types to remote servers. The top 10 Android malware samples that were detected in Q3, 2015 are as follows:
- Android.Airpush.G
- Android.Smsreg.DA
- Android.Sprovider.A
- Android.Ztorg.A
- Android.Wroba.A
- Android.Leech.E
- Android.Rootnik.C
- Android.Reaper.A
- Android.CallPay.A
- Android.Senrec.A
Apart from these top 10 Android malware samples, there were other forms of Android malware also discovered that raised alarm bells. Some of these samples were capable of bypassing CAPTCHAS on app stores and hence they could pose as fake apps on legitimate app stores. Some other notable forms of Android malware also had the capability of cloning social networks and games in order to convince people to download the apps.
The Quick Heal Android Threat Report for Q3, 2015 reemphasizes that most of the detected file types and methodologies have been foreseen by security analysts. However, this does not mean that users have been immune from them. It is staggering to see that a large number of people are still running very old Android versions without adequate security solutions installed. So the potential for damage by malware authors is indeed very high. With the in-depth details from the Threat Report, we will be able to delve further into the nature of this malware and the damage it can do with regards to user security and privacy.


268 Comments
I am happy with quick heal.
please remove the malware from my computer
Hi Gour,
May we request you to contact our technical support team. They will help you resolve this issue as soon as possible. You can reach them here – https://www.quickheal.co.in/submitticket.
Regards.
remove the malaware from my computer
Hi,
Thanks for writing in. Our support team can help you with this:
1. Kindly submit your query at https://bit.ly/Askus
2. You can also contact them at 0-927-22-33-000
3. Alternatively, you can chat with our engineers by visiting https://bit.ly/QHSupport
Regards.
Please solve the problem.The message”WEBSITE IS BLOCKED FOR YOUR PROTECTION” shows again and again when i want to proceed for browsing and this is problematic for browsing.Please solve the problem immediately.
Hi Saumen,
Thanks for writing in. Our support team can help you with this:
1. Kindly submit your query at https://bit.ly/Askus
2. You can also contact them at 0-927-22-33-000
3. Alternatively, you can chat with our engineers by visiting https://bit.ly/QHSupport
Regards.
remove the malware from my computer
Hi Resy,
May we request you to contact our technical support team. They will help you resolve this issue as soon as possible. You can reach them here – https://www.quickheal.co.in/submitticket.
Regards.
update quick heal internet security
Hi Madhusudan,
May we request you to contact our technical support team. They will help you resolve this issue as soon as possible. You can reach them here – https://www.quickheal.co.in/submitticket.
Regards.
thanks. please update us time to time to improve security system.
Good antivirious Muje Aacha Laga Mera PC Bhi Sahi Chal Raha Hai
Happy
In MSworld a virse change letter show other latter with blue under score.
Please tell us solution on 09413560875
Hi Pradeep,
Thanks for writing in. Our support team can help you with this:
1. Kindly submit your query at https://bit.ly/Askus
2. You can also contact them at 0-927-22-33-000
3. Alternatively, you can chat with our engineers by visiting https://bit.ly/QHSupport
Regards.
i am very happy
kindly check my report
Hi Chirag,
Thanks for writing in. Our support team can help you with this:
1. Kindly submit your query at https://bit.ly/Askus
2. You can also contact them at 0-927-22-33-000
3. Alternatively, you can chat with our engineers by visiting https://bit.ly/QHSupport
Regards.
no update
i am very happy quick heal
looking for antyvirus
Dear Sir,
I would like to complaint in my mobile eit show update but it’s not possible and also it show out dated I purchase the mobile recently and quick heal activated also same day and validity shows up to one year but it’s not working properly please check and inform.
Hi Kumaraswamy,
Thanks for writing in. Our support team can help you with this:
1. Kindly submit your query at https://bit.ly/Askus
2. You can also contact them at 0-927-22-33-000
3. Alternatively, you can chat with our engineers by visiting https://bit.ly/QHSupport
Regards.
Dear Sir,
I would complaint about quick heal due to I activated last 2 month back when I purchase the New phone but it’s required update and its show out of service please check and inform asap.
Hi Kumaraswamy,
Thanks for writing in. Our support team can help you with this:
1. Kindly submit your query at https://bit.ly/Askus
2. You can also contact them at 0-927-22-33-000
3. Alternatively, you can chat with our engineers by visiting https://bit.ly/QHSupport
Regards.
Dear Sir,
Quick heal is very fantastic Anti Virus to remove Viruses but it does not remove MS DOS virus from the computers. if this software does remove of MS DOS viruses, It make very valuable Antivirus.
Thanks & Regards
N.A.Gadri
remove android malware from computer
Hi Ashutosh,
May we request you to contact our technical support team. They will help you resolve this issue as soon as possible. You can reach them here – https://www.quickheal.co.in/submitticket.
Regards.
I am happy with QUICK HEAL
It’s Good scans well.
please remove the mamaware From my computer, and always update my software
Hi Ajit,
May we request you to contact our technical support team. They will help you resolve this issue as soon as possible. You can reach them here – https://www.quickheal.co.in/submitticket.
Regards.
It is very good I am using this quick heals from nearly 10 years onwards very nice
I have quick heal security. But I’m always afraid that someone is hacking my fone.Is it possible?
Hi Sandeep,
It is possible, but if you follow the right security tips and precautions then you can keep your phone secure.
Regards.
Quickheal save and protect my computer, so i stay tension free.
i am using this first time.
Its really good
i am so happy…
quick heal anti pro
We are using Android in our mobile phones & frequently connects it with our PC where we are using the Great Quick Heal. I hope, it will remove malwares successfully.
Same hear happy with it
PLESAE KINDLY CHECK MY REPORT
Hi Rajib,
May we request you to contact our technical support team. They will help you resolve this issue as soon as possible. You can reach them here – https://www.quickheal.co.in/submitticket.
Regards.
Thank you for your venture.
best security but daily update impossible
please sir help me three days after update fail why
Please solve the problem.The message”WEBSITE IS BLOCKED FOR YOUR PROTECTION” shows again and again when i want to proceed for browsing and this is problematic for browsing.Please solve the problem immediately.
Hi Balram Kumar,
I just gone through your post and if you are still searching for a solution, you may please follow few steps as mentioned below.
1. Update your Quick Heal security solution followed by 3 different scan cycles – Boot Time Scan, Memory Scan & Full System Scan.
2. Also follow the step by step procedure as mention in this link https://malwaretips.com/blogs/remove-browser-redirect-virus/ (the page runs in secured protocol, so, you may open the link without hesitation).
All the best.
Regards,
Sambaran
(1) Please solve the problem.The message”WEBSITE IS BLOCKED FOR YOUR PROTECTION” shows again and again when i want to proceed for browsing and this is problematic for browsing.Please solve the problem immediately.
(2) When i open any sight some some other site automatically opens that i don’t want. i close this unwanted site 2-3 times after that my desired site opens. please help.
this happens from, i think last 01 week. please help solve the problem.
due to this i am in confusion that site is malware or something.
when i open something something else automatically opens then i close that unwanted after that desired site opens
Hi Balram,
May we request you to contact our technical support team. They will help you resolve this issue as soon as possible. You can reach them here – https://www.quickheal.co.in/submitticket.
Regards.
I am happy with quick heal.
remove the malware in my computer
Hi Skm Basha,
May we request you to contact our technical support team. They will help you resolve this issue as soon as possible. You can reach them here – https://www.quickheal.co.in/submitticket.
Regards.
best security.
my quick heal total security not updated automatically?
Hi Jitesh,
May we request you to contact our technical support team. They will help you resolve this issue as soon as possible. You can reach them here – https://www.quickheal.co.in/submitticket.
Regards.
rahul sir please help me
daily update is impossible
Hi Janu,
May we request you to contact our technical support team. They will help you resolve this issue as soon as possible. You can reach them here – https://www.quickheal.co.in/submitticket.
Regards.
Information is worth of note and very essential.
best
thanks. please update us time to time to improve security system.
No Update
Hi,
May we request you to contact our technical support team. They will help you resolve this issue as soon as possible. You can reach them here – https://www.quickheal.co.in/submitticket.
Regards.
It is best for android sequrity
I m happ with quick Heal Antivirus….
Good Information given. Thank you very much.
it is best Android sequrti
Quick Heal
Thanks
best security but daily update impossible
quickheal is not much useful to remove the virus/malwares because it is not functioning, properly
Sir solutions my mobile virus
Agitate Kumar.
Hi Aditya,
May we request you to contact our technical support team. They will help you resolve this issue as soon as possible. You can reach them here – https://www.quickheal.co.in/submitticket.
Regards.
Good
it is bast for android or pc sequrity remove malwara my android and pc
Quick heal aniti virus excellant working brother
my dear rahul excellent working anti virus Quick heal
Please rectify the problem very uegently .The message by quickheal protection mentioning”WEBSITE IS BLOCKED FOR YOUR PROTECTION” shows again and again when i want to browse. please help me regarding issue and solve the problem immediately.
Hi Sandesh,
May we request you to contact our technical support team. They will help you resolve this issue as soon as possible. You can reach them here – https://www.quickheal.co.in/submitticket.
Regards.
HAPPY TO
Take necessary action to protect my laptop.
Hi,
May we request you to contact our technical support team. They will help you resolve this issue as soon as possible. You can reach them here – https://www.quickheal.co.in/submitticket.
Regards.
remove the malaware from my computer
Hi Sudip,
May we request you to contact our technical support team. They will help you resolve this issue as soon as possible. You can reach them here – https://www.quickheal.co.in/submitticket.
Regards.
Well thanks. I’ll check my phone. It called to me as a reminder that all devices are at risk. I hope there is no problem. If there were I feel like it would be handled well. Good security. Happy.
nic
thankyou quick hil
best best…………………………………….
Please remove all the Adware from my Computer
Hi K.T.Mariapparajan,
May we request you to contact our technical support team. They will help you resolve this issue as soon as possible. You can reach them here – https://www.quickheal.co.in/submitticket.
Regards.
Best sequrity
It provide best securities
no update
Hi Rakesh,
May we request you to contact our technical support team. They will help you resolve this issue as soon as possible. You can reach them here – https://www.quickheal.co.in/submitticket.
Regards.
Best sequrity
Best secuirty
I hope that my computer will be made free from MALWARE.
I am happy to use quick heal.
A veygod antyvirous
best security
no update
Hi Rahul,
May we request you to contact our technical support team. They will help you resolve this issue as soon as possible. You can reach them here – https://www.quickheal.co.in/submitticket.
Regards.
thanks
it provide best security in my computer
good product . valid upto 16thjuly 2016. Internet centre stop
Eroor code reced id-1004 when update my computer today i3e 09/11/2015
Hi Kannepalli,
May we request you to contact our technical support team. They will help you resolve this issue as soon as possible. You can reach them here – https://www.quickheal.co.in/submitticket.
Regards.
good quality regularly update computer valid upto 16th july 2016. but todat internet centre of quick heal is stopped update
tnx a lot quick heal
I hope that my computer will be made free from MALWARE
My computer need free from malware
Hi Lakhote B.N.,
May we request you to contact our technical support team. They will help you resolve this issue as soon as possible. You can reach them here – https://www.quickheal.co.in/submitticket.
Regards.
My mobile is always hangs
Hi Sunil,
May we request you to contact our technical support team. They will help you resolve this issue as soon as possible. You can reach them here – https://www.quickheal.co.in/submitticket.
Regards.
Mera quick hel update now bata raha hai plese help me
Hi Anish,
Please update your Quick Heal software when you see such a message.
Regards.
please add adware cleaner too …
NICE WORK MY QUICLHIAL
thadani sir help me daily update net problem
Hi Janu,
May we request you to contact our technical support team. They will help you resolve this issue as soon as possible. You can reach them here – https://www.quickheal.co.in/submitticket.
Regards.
no action required
I hope that there should be no threat at all from any kind of MALWARE.
dealy update imposible
Hi Karamat,
May we request you to contact our technical support team. They will help you resolve this issue as soon as possible. You can reach them here – https://www.quickheal.co.in/submitticket.
Regards.
BUT I AM HAPPY
I LIKE THE BEST ANTIVIRUS
QUICK HEAL
i am using quick heal total security antivirus but every 3-4 day he wants to updated now. so what i am doing
Hi Shashank,
Please update your Quick Heal software when you see this message. This protects your device against the latest virus signatures that are discovered around the world.
Regards.
sir, i cannot update my anti virus quick heal , i would seek help from you, kindly sent me the solution for the problem sir.
Hi Albert,
May we request you to contact our technical support team. They will help you resolve this issue as soon as possible. You can reach them here – https://www.quickheal.co.in/submitticket.
Regards.
nice all ……
nice …..
protect my laptop from privacy error
Hi Prakash,
May we request you to contact our technical support team. They will help you resolve this issue as soon as possible. You can reach them here – https://www.quickheal.co.in/submitticket.
Regards.
first update problam hai update setup file milne se good
Hi,
May we request you to contact our technical support team. They will help you resolve this issue as soon as possible. You can reach them here – https://www.quickheal.co.in/submitticket.
Regards.
sir while playing video it automatically stops as shown on the screen as speed :0.02X.
and in any MS-office if we enter the one key it takes repetedly under score . so pls slove my computer problems sir
Hi Sharath,
May we request you to contact our technical support team. They will help you resolve this issue as soon as possible. You can reach them here – https://www.quickheal.co.in/submitticket.
Regards.
i Formated my System Recently, Instaled Quickheal its not Updating, please send update
Hi Srinivas,
May we request you to contact our technical support team. They will help you resolve this issue as soon as possible. You can reach them here – https://www.quickheal.co.in/submitticket.
Regards.
last 15 days facing problem for quick updates in laptop submitted
ticket under urgent priority but no respond.
LNY-765-57418 OF 08 JUNE 2015 02:29 PM FAZAL SHAIKH
TREAT AS MOST URGENT
Hi Baliraj,
May we request you to contact our technical support team. They will help you resolve this issue as soon as possible. You can reach them here – 0-92722 33000.
Regards.
Thanks for your valuable informations
Have I got adueqate Quick Heal protection ?
Hi Rodney,
If your Quick Heal product is updated to the latest version, then you do have adequate protection.
Regards.
Dear sir
when we are browsing earlier, on one click on internet browser firefox in any box (empty) to type it will switch over to new tab. what was the problem.
Hi Sahoo,
May we request you to contact our technical support team. They will help you resolve this issue as soon as possible. You can reach them here – https://www.quickheal.co.in/submitticket.
Regards.
Best Antivirus but daily update is not possibal soo doind sam thing
My computer should be free from malware and any other virus
how could i be safe from these kinds of melaware .plz suggest …………….
Hi Sandip,
Quick Heal detects the presence of all these malware types and keeps your device safe against them. So keep your virus database updated to the latest versions for maximum protection.
Regards.
I like to say my pc is free from antivirus problem
it is best security but daily update system is too much difficult.
Happy
Can I use Quickhear for my windows mobile lumia 540?
Hi Binaya,
The Quick Heal apps are available only on Android and iOS as of now. We do not support the Windows Phone platform currently.
Regards.
nice
Dear sir
i like the quick heal antivirus, but there is some problem with it. I think this is my laptop slow. Sometimes it’s very difficult to work on pc. please give me solution to solve my problem.
Thanks.
Hi Meentu,
May we request you to contact our technical support team. They will help you resolve this issue as soon as possible. You can reach them here – https://www.quickheal.co.in/submitticket.
Regards.
nice project
How can i remove Virus like Desktop.ini Created everywere ????
Hi Jashwant,
May we request you to contact our technical support team. They will help you resolve this issue as soon as possible. You can reach them here – https://www.quickheal.co.in/submitticket.
Regards.
plz plz plz remove that threat plz plz
regular flash from quick heal internet security that”WEB SITE IS BLOCK FOR YOUR PROTECTION”.”WEB SITE YOU ARE VISITING MAY BE HARM FUL””IF YIU STILL WISH TO VISIT THE WEB SITE CLICK HERE AND TRY AGAIN””IF YOU THINK THIS IS A MISTAKE,TO REPORT CLICK HERE.”
We are getting this type regular message ,even if we are in gmail through CROME or at our banking site.
This message is not responding any command.please make us relief from regular flash message which is ditrubing our works.
Hi Tapas,
May we request you to contact our technical support team. They will help you resolve this issue as soon as possible. You can reach them here – https://www.quickheal.co.in/submitticket.
Regards.
Good version till now seen we are usingit to system a d to mobile also thankyou
I m happy with quick heal +919867233061
its best securiti for mobile.
Best security
Thanks alert for you
Please remove all malware n other things which do not allow system to run smoothly.
Regards,
Pradyot Mankodi
Please update app lock on phone.
I am very sad about that I can’t lock my app plz help me…….other then I am happy with quickheal…..
Hi Rajkumar,
The app lock feature is available in our Fonetastic app. Please visit this link for more information – https://www.quickheal.co.in/home-users/quick-heal-fonetastic-pro. You can also find and download the app from Google Play.
Regards.
FINE
I am happy with Quick heal ,Now it comes in my screen to update to version 16 pro I clicked OK but noresult . The previous version is not updating what shall I do ? Please guide me if you can.
Hi Manoranjan,
Please follow the steps on this link for completing this – https://www.quickheal.co.in/upgrade/.
Regards.
best secuirty of Q
very nice antivirus
M facing again n again problem In go SMS pro theam
Hi Maan,
May we request you to contact our technical support team. They will help you resolve this issue as soon as possible. You can reach them here – https://www.quickheal.co.in/submitticket.
Regards.
I think its best security app that not used before in my phone
Very nice antivirus
Nice
send reply after copletion of instal
Hi Gopal,
Once installations are complete, notifications are shared regarding the same.
Regards.
Not updating from last 3 days
Hi Mahesh,
Apologies for the inconvenience. Please let us know if the problem still persists now. If it does, please submit a ticket with our technical support team by visiting this link – https://www.quickheal.co.in/submitticket.
Regards.
I AM HAPPY WITH QUICK HEAL
my pc not service gurdian anitivirus
plz come to help bayana distt.bharatpur rajasthan
mobile no. 8290370268
Hi Anil,
May we request you to contact our technical support team. They will help you resolve this issue as soon as possible. You can reach them here – https://www.quickheal.co.in/submitticket.
Regards.
I am enjoining with quickheal mobile security
it protect my device from all the major priblems
Please improve the update…………. It takes a little longer to update …………..would be better if the update was faster….
Hi Karna,
Thank you for your feedback. We will surely improve the size of our updates as time goes by and polish them further.
Regards.
I like it
Nice ant virus
Its a very good security.And its soo good for others securities
Good antivirious Muje Aacha Laga Mera PC Bhi Sahi Chal Raha Hai
Dear Sir,
I would complaint about quick heal due to I activated last 2 month back when I purchase the New phone but it’s required update and its show out of service please check and inform asap.
Hi Saakib,
May we request you to contact our technical support team. They will help you resolve this issue as soon as possible. You can reach them here – https://www.quickheal.co.in/submitticket.
Regards.
It is best for android sequrity
best antivirus strong
Thanks….update my quick heals …best protected
Hi Kishorkumar,
If you wish to upgrade your Quick Heal to the latest version, please visit this link – https://www.quickheal.co.in/upgrade/.
Also, if you wish to download the latest virus database update, then you can visit this link – https://www.quickheal.co.in/quick-heal-antivirus-updates-download.
Regards.
Nice app
Updates not done since 4 days
Hello,
Please check again if the updates are working and let us know about the same. If not, then please contact our technical support center by visiting this link – https://www.quickheal.co.in/submitticket.
Regards.
I am satisfied with Quick Heal’s Performance.Effective
Is the best for Anroaid security
best antivirus
After installing quick heal iam not bothered about my system even I suje step in our office very good anti virus
Very Best Antivirus
Jst nw I received a message ” evolution of android quick heal threat report” what does this mean ? Is my phone is nt secure? Is Dr any threat in my phone. And it also shows tap to increase the security..wt shd I do Plz reply me sn
Hi Mohsin,
The blog post shares some details from the Q3 threat report which talks about the popular strains of malware over Android. If your Quick Heal is updated to the latest version, then your device is protected.
Regards.
Dear sir,
My Lenovo a7000 mobile lost and I am using quickheal security. Can u track this my mobile for quickheal system…
Hi Yuvraj,
We hope that you have lodged a complaint with the local police station, and disabled your SIM card. We’d recommend you to visit https://mydevice.quickheal.com/rsvc/login | Here you can track your mobile’s location.
Regards,
I’m getting malware daily so,please remove the malware from my mobile
Hi Franklin,
Are you using any mobile security app in your device?
Regards,
How can remove my malware in my experiya M dual
Because mobile functions is very slow conditions
Please solution
Hi Avinash,
Are you using any mobile security app?
Regards,
I’m happy using this
Good performance
I am using app my mobile
its not getting update . always says Not Responding . how i solve it..
Hi Shivam,
May we request you to contact our technical support team. They will help you resolve this issue as soon as possible. You can reach them here – https://www.quickheal.co.in/submitticket.
Regards.
Please remove malaware from my mobile
Hi Shubham,
May we request you to contact our technical support team. They will help you resolve this issue as soon as possible. You can reach them here – https://www.quickheal.co.in/submitticket.
Regards.
I am using app my mobile
I m using this app
Please help me.
My mobile has various error generated,
engriks,measures,mobileocr,battery control,catstudio,etc..
My mobile has internet data will be on to hang full mobile & automatically harmful app installed.
I’m not installed but automatically installed.
Hi Denish,
May we request you to contact our technical support team. They will help you resolve this issue as soon as possible. You can reach them here – https://www.quickheal.co.in/submitticket.
Regards.
I rely on QH Eveyday.. My Latop feels safe including My Phone.
Thank You Quick Heal……..
Hi
I am Parth
My problem is mobile locked
Hi Parth,
May we request you to contact our technical support team. They will help you resolve this issue as soon as possible. You can reach them here – https://www.quickheal.co.in/submitticket.
Regards.
Please secure my mi4i phone from virus
Hi Ramakant,
May we request you to contact our technical support team. They will help you resolve this issue as soon as possible. You can reach them here – https://www.quickheal.co.in/submitticket.
Regards.
i love quick heal.quick heal is best antivirus. i love you quick heal.
It’s not work properly in android fon
Hi Vidhyasagar,
May we request you to contact our technical support team. They will help you resolve this issue as soon as possible. You can reach them here – https://www.quickheal.co.in/submitticket.
Regards.
It’s very good
All thing is ok
Working good
Before installing the app my phone has various problem of viruses
After installing quick heal most problems has been solved.
I am happy with quick heal
I’m very much secure with quickheal
quick heal not be update
Hi Ajay,
May we request you to contact our technical support team. They will help you resolve this issue as soon as possible. You can reach them here – https://www.quickheal.co.in/submitticket.
Regards.
Thank you
Quickheal is very good indeed.
Please remove threat
Hi Shakti
Can you share some more details about the threat that you are facing. May we also request you to contact our technical support team. They will help you resolve this issue as soon as possible. You can reach them here – https://www.quickheal.co.in/submitticket.
Regards.
i want to scan my android device so how it is possible…
please provide some useful tips …
quickheal is my favourite virus protector
Hi Kesur,
You can download the Quick Heal Mobile Security app. This is a free app and you can download it from the Google Play store. It will allow you to easily scan your Android device and it has several other great features as well.
Regards.
Hey Quick Heal, when is QH 2016 releasing ? Every year we get to see new version in November but this year it’s already December but next version has not been released.
Hi Himanshu,
We will be releasing details for the new version in the coming weeks, so please stay tuned for more information.
Regards.
Will there be beta testing ?
I am very satisfied to use Quick Heal..
I like this App. & I want say thank.
It is the best of threat didectin solution for android mobile and very happy for this app…
Quick Heal is Very Good Indeed…
Hi,
I am a user of QH (Internet Security).
It is valid up to May 2018.
Recently I purchased MOTO G2 (Android 5.0).
Suggest QH product for the same.
Thanks
Hi Shyam,
You can visit the Google Play Store and install one of our mobile security apps for your device’s protection and performance. You can view the apps and their benefits here – https://www.quickheal.co.in/home-users.
Regards.
Pls help me to remove virus from my android device(ZenFone5) I am using Google chrome.sometimes some messages are showing with alarm bell. That is like a YOUR DEVICE IS AFFECTED VIRUSES.and other messages also. Sometimes I can’t go back from browser. What can I do????
Help pls.
Hi,
May we request you to contact our technical support team. They will help you resolve this issue as soon as possible. You can reach them here – https://www.quickheal.co.in/submitticket.
Regards.
Quick heal is good
Thanks qhil antivirus
Please , remove malware from my device
Hi Trilok,
Thanks for writing in. Our support engineers would gladly help you with this issue. Please visit https://bit.ly/QHSupport and click ‘Chat with Us’. You can also raise a ticket at https://bit.ly/Askus and we will get back to you at the earliest.
Regards.
Quickheal is good