How Point of Sale (PoS) Malware Steals Credit Card Data
The Quick Heal Quarterly Threat Report for the second quarter of 2015 indicated a massive rise in the number of malware samples that afflicted the Windows platform across the world. This trend can be attributed to the fact that malware authors have started propagating their malicious software variants to all corners of the globe, and also the fact that a lot of people still operate their PCs without effective antivirus software and with unpatched operating systems and software.
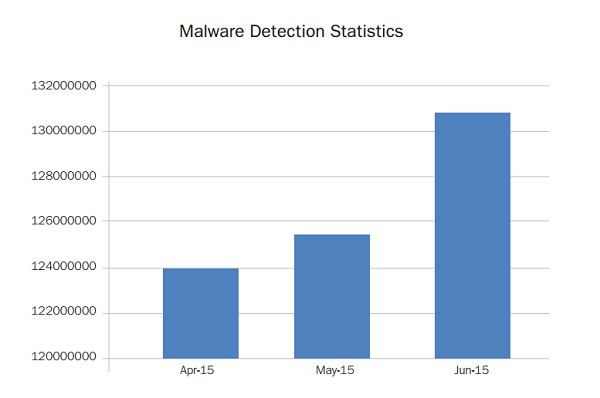
In the months of April, May and June 2015, the Quick Heal Threat Research Labs received many Windows malware samples, and these are highlighted in the complete report which is now available. Moreover, it was also found that a majority of detections occurred on 32-bit machines. This has led us to believe that people looking to buy new machines should consider purchasing 64-bit machines as these have fewer malware threats in proportion.
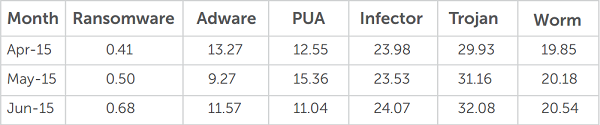
Some other categories of Windows malware that were detected were found over the following categories:
- Ransomware
- Adware
- Potentially Unwanted Applications (PUAs)
- Infectors
- Trojans
- Worms
- Exploit kits
- Point of Sale (PoS) malware
Key findings of the Quick Heal Threat Report Q2, 2015 for Windows
- Over the Windows platform, Quick Heal detected around 65 million malware samples per month in the second quarter of 2015.
- Moreover, we have found that 74% of Windows malware samples detected run on 32-bit machines. In most cases, these in-the-wild variants are not supported on 64-bit systems.
- In Q2, 2015 the most number of malware threats were detected in the Trojan category. Trojans enter vulnerable machines through trusted software or downloads, or other propagation techniques.
- The most common malware sample detected was LNK.Exploit.Gen, which constituted 26% of the total samples.
- Adware and Malvertising remain top attack vectors for malware authors and malicious software samples. Adware samples are also expected to use browser hijacking techniques in the near future.
- New Point of Sale (PoS) malware families have also been found in Q2 2015 and these steal debit/credit card details from PoS terminals of merchants.
- Threat authors have moved their attention to the banking sector and common banking Trojans are expected to make use of spear phishing emails, social engineering tactics, and RAT (Remote Access Control) tools for remotely controlling ATM machines.
Future trends for Windows malware over the coming months
Adware: Unwanted caretaker
Online ads are getting more personal and the Internet browsing habits of users are under the radar of malware authors. They use this monitoring to deliver ads that carry malicious intent and this process is known as Malvertising. This is done without the consent or knowledge of users and going forward, browser hijacking tricks are going to come under the spotlight. This will enable malware authors to collect personal data and browsing habits of victims more accurately.
Ransomware: More variants, more encryption, more profits
Ransomware has become a very profitable business model for attackers and this trend will continue further. Old ransomware variants are also expected to come back with new modifications. The recent wave of crypto-ransomware samples showcased advanced evasion and encryption tricks and their ability to attack cloud storage services is also expected to take place. Targeting specific industry sectors like banking, healthcare and education is another possible source of income for ransomware writers.
Spamming to continue as an effective infection vector
Most of the ransomware variants encountered in Q2 2015 spread and propagated via spam emails and had improved security evasion and bypass techniques. CryptoWall 3.0 and CRYPVAULT crypto-ransomware are two such ransomware samples that employed noticeable techniques. Such samples are expected to use malicious JavaScript files and complex obfuscation tricks to evade detection from security software. Once done, they will also connect to remote C&C servers and download additional malicious payloads.
More specific banking Trojans
Threat authors have now moved their attention and efforts to the banking sector, as this is a home for money. So, malware families with more advanced techniques are expected to hit machines soon. Spear phishing emails and social engineering tactics can also be used as carriers for delivering banking malware to organizations. The use of RAT (Remote Access Control) tools for remotely controlling ATM machines is also expected to lead to the exposure of sensitive card data.
The Quick Heal Quarterly Threat Report Q2, 2015 goes into the details of the popular malware samples over the Windows platform. The number of samples involved is very large and this is a cause for concern not just for users, but for security service providers as well. This makes the need for security awareness and effective security measures greater than ever.
You can also read about the key highlights of the Android threat report here.



79 Comments
I am using Quickheal. What care do I have to take.
Hi Paras,
My two suggestions are:
1. Pay cash as often as possible when you make purchases.
2. If you must use a card, have a special card for transactions and keep the account balance or credit limit of that very low.
Regards.
Dear Sir,
Feeling safe with Quickheal.
Sadruddin
this info is very useful.
i want to say that QUICK HEAL is the best antivirus so far. i have used it and am attesting to it. i have been recommending it to people including my colleagues in the office
not work anti virus
Hi Sumant,
You are requested to contact our support center to resolve this issue. You can:
1. Call us on 0-927-22-33-000
2. Submit a ticket here – https://www.quickheal.co.in/submitticket
3. Chat with us here – https://www.quickheal.co.in/quick-heal-support-center
Regards.
dear sir my pc win8 many adware cant remove browser start add start
how i manage
Hi Vimal,
Our Support Team can help you solve this issue:
1. You can submit your query at https://bit.ly/Askus. The Team will get back to you with a solution.
2. You can also contact them at 0-927-22-33-000.
3. Alternatively, you can chat with our engineers by visiting this link >> https://bit.ly/QHSupport >> Chat with Us
Regards,
Hi
POS malware sounds scary
How do we protect ourselves from POS malware?
Hi Amit,
My two suggestions are:
1. Pay cash as often as possible when you make purchases.
2. If you must use a card, have a special card for transactions and keep the account balance or credit limit of that very low.
Regards.
VERY USEFUL INFORMATION………………
My Comment is related with free android apps given by chetah mobile like battery doctor, Screen lock, subborn trogen killer, antivirus. Are they genuine ? Kindly say something about it. Thanks
Hi Mahesh,
If these apps are available on Google Play, you can go ahead and install them. They should be fine.
Regards.
I am using your product for the past 2years or so. kindly tell me
when the product is to be renewed
Hi,
When the product expiry date is near you will receive notifications about the same. It is recommended that you renew the product at that time.
Regards.
I LIKE THIS ANTIVIRUSH………………
so what is the way to avoid this kind of attack what measures we must take
Hi Rutul,
The best thing to do is to try to avoid card payments as much as possible. Try to pay by cash often or use a card which has less balance in it and is used only for shopping purposes.
Regards.
I am facing an adware problem. Often when I am browsing a site, a new tab “www.adsmatte.com” opens automatically.It very irritating. It also stops or delays online payments for bill payments and shopping etc. I’m using Quickheal Total Security, then why it is not capable to remove this adware?
Hi Gurmukh,
You are requested to contact our support center to resolve this issue. You can:
1. Call us on 0-927-22-33-000
2. Submit a ticket here – https://www.quickheal.co.in/submitticket
3. Chat with us here – https://www.quickheal.co.in/quick-heal-support-center
Regards.
Happy to note about information. Glad to note that Quick heal has ways and means to stop/prevent the same from corrupting the computers.
this is good
good
Excellence a virus
Very happy to know this. Please renew my product. Already Rs 849/- has been collected from me. Serve better.
Hi Raju,
If the payment has been made from your end, the product will be renewed soon. The speed will depend on the channel chosen for renewal. Online renewals will show up immediately but other modes will take longer.
Regards.
supper I like the quickheal
If credit card data is being stolen at POS by the Shops and Merchants, it is extremely dangerous to use our Credit/Debit Cards.
Either they need to be cross verified by finger prints OR the POS merchant needs to declare that they are safe to deal from data security point of view. If the machines are secured by some organisation like Quick Heal and certified, it could be a bit better. And the establishment can also advertise that they are Quick Heal certified.
It is a new avenue for business of Quick Heal slso.K83
Thanks Sir And I Am In Troubled With Some My Own Issuing Please Sir Help Me Best .
Hi Sanjay,
You are requested to contact our support center to resolve this issue. You can:
1. Call us on 0-927-22-33-000
2. Submit a ticket here – https://www.quickheal.co.in/submitticket
3. Chat with us here – https://www.quickheal.co.in/quick-heal-support-center
Regards.
yes
my pen drive in infected of virus but my quick heal total security in not scanned . why i am expense my purchase quick heal total security please solve my problems as soon as possible. thanks
Hi Surjeet,
You are requested to contact our support center to resolve this issue. You can:
1. Call us on 0-927-22-33-000
2. Submit a ticket here – https://www.quickheal.co.in/submitticket
3. Chat with us here – https://www.quickheal.co.in/quick-heal-support-center
Regards.
update problem
Hi Shoibur,
You are requested to contact our support center to resolve this issue. You can:
1. Call us on 0-927-22-33-000
2. Submit a ticket here – https://www.quickheal.co.in/submitticket
3. Chat with us here – https://www.quickheal.co.in/quick-heal-support-center
Regards.
MY LAPTOP IS SHOWING SIGNS OF COMPROMISED SECURITY. MY QUICK HEAL IS NOT GETTING UPDATED.THE ICON IS STAYING ORANGE INSTEAD OF TURNING GREEN IN SPITE OF RUNNING THE UPDATE AND IT IMMEDIATELY SAYING THAT MY SYSTEM IS UPTODATE!!
Hi Dhruv,
You are requested to contact our support center to resolve this issue. You can:
1. Call us on 0-927-22-33-000
2. Submit a ticket here – https://www.quickheal.co.in/submitticket
3. Chat with us here – https://www.quickheal.co.in/quick-heal-support-center
Regards.
not update
Hi Bappa,
You are requested to contact our support center to resolve this issue. You can:
1. Call us on 0-927-22-33-000
2. Submit a ticket here – https://www.quickheal.co.in/submitticket
3. Chat with us here – https://www.quickheal.co.in/quick-heal-support-center
Regards.
nice
not getting update inspite of trying again and again.. irritating
Hi Manvendra,
You are requested to contact our support center to resolve this issue. You can:
1. Call us on 0-927-22-33-000
2. Submit a ticket here – https://www.quickheal.co.in/submitticket
3. Chat with us here – https://www.quickheal.co.in/quick-heal-support-center
Regards.
MERA ANTI VIRUES HAMESA RED HI RAHTA H UPDATE KARNE KE BAAD BHI SOLUTION BATAYE
Hi Natwar,
You are requested to contact our support center to resolve this issue. You can:
1. Call us on 0-927-22-33-000
2. Submit a ticket here – https://www.quickheal.co.in/submitticket
3. Chat with us here – https://www.quickheal.co.in/quick-heal-support-center
Regards.
FROM LAST 5 YEARS NOT FORMATTED ANY DESKTOP / LAPTOP DUE TO CORRUPT OR VIRUS ATTACK,
ALL BIG THANKS TO QUICK HEAL ( OBVIOUSLY!!! TO ME ALSO FOR A GREAT DECISION).
TODAY SERVER & LAPTOP SHOWS “PROTECTION OUT OF DATE” BUT AFTER CLICKING UPDATE NOW – SHOWS ” UP TO DATE” .. & AMBER ICON IS SHOWS AS IT IS.
CUSTOMER CARE LINE IS COMING BUSY FROM LAST 1 AND HALF HOUR……
PLEASE ARRANGE TO HELP BY E-MAIL OR CALL..
THANKS
PRABHU
Hi Natwar,
You are requested to contact our support center to resolve this issue. You can:
1. Call us on 0-927-22-33-000
2. Submit a ticket here – https://www.quickheal.co.in/submitticket
3. Chat with us here – https://www.quickheal.co.in/quick-heal-support-center
Regards.
Its may be best working…..
MERA ANTI VIRUES HAMESA RED HI RAHTA H UPDATE KARNE KE BAAD BHI SOLUTION BATAYE
Hi Subash,
Our Support Team can help you solve this issue:
1. You can submit your query at https://bit.ly/Askus. The Team will get back to you with a solution.
2. You can also contact them at 0-927-22-33-000.
3. Alternatively, you can chat with our engineers by visiting this link >> https://bit.ly/QHSupport >> Chat with Us
Regards,
My update has stopped after 16/07/2015. In Anti-malware scanning one adware was detected and cleaned. Still update is not done both in auto and manual. Please advice.
Hi C R,
Our Support Team can help you solve this issue:
1. You can submit your query at https://bit.ly/Askus. The Team will get back to you with a solution.
2. You can also contact them at 0-927-22-33-000.
3. Alternatively, you can chat with our engineers by visiting this link >> https://bit.ly/QHSupport >> Chat with Us
Regards,
Fine quick-Heal-Antivirus
Quick Jeal Total Security last up date 16 july 2015 but today is not update. Please help Me.
Hi Subhasis,
Our Support Team can help you solve this issue:
1. You can submit your query at https://bit.ly/Askus. The Team will get back to you with a solution.
2. You can also contact them at 0-927-22-33-000.
3. Alternatively, you can chat with our engineers by visiting this link >> https://bit.ly/QHSupport >> Chat with Us
Regards,
please reply–why I am not able to UPDATE
Hi Pradyut,
Our Support Team can help you solve this issue:
1. You can submit your query at https://bit.ly/Askus. The Team will get back to you with a solution.
2. You can also contact them at 0-927-22-33-000.
3. Alternatively, you can chat with our engineers by visiting this link >> https://bit.ly/QHSupport >> Chat with Us
Regards,
Quick Heal is the best among all which I have felt. I am using it for last 6 years and never any problem arises.
I have two Question:
1. I am using Quick Heal Total Security. I Oftanly Recharge by my Debit Card in Paytm or Freecharge Website. Both Web site are safe for online transaction? and If not then Quick Heal Protect us for this type of attact?
2. And how to know that this website is protected or not?
Hi Amish,
Yes, Quick Heal Total Security protects your from fake and malicious websites. You can know a website it safe or not by checking its URL. A secured website always begins with ‘https’ and has a padlock symbol (green) to it.
Regards,
I use quick hell anty virous sofware in all pc but last three days virus protection ont update since 3 days.
MY ALL PC QUICK HEAL IS NOT GETTING UPDATED.THE ICON IS STAYING ORANGE INSTEAD OF TURNING GREEN IN SPITE OF RUNNING THE UPDATE AND IT IMMEDIATELY SAYING THAT MY SYSTEM IS UPTODATE!!
Hi Viral,
Our Support Team can help you solve this issue:
1. You can submit your query at https://bit.ly/Askus. The Team will get back to you with a solution.
2. You can also contact them at 0-927-22-33-000.
3. Alternatively, you can chat with our engineers by visiting this link >> https://bit.ly/QHSupport >> Chat with Us
Regards,
My Computer no up-date. please solve my problems as soon as possible. thanks
Hi Sankar,
Our Support Team can help you solve this issue:
1. You can submit your query at https://bit.ly/Askus. The Team will get back to you with a solution.
2. You can also contact them at 0-927-22-33-000.
3. Alternatively, you can chat with our engineers by visiting this link >> https://bit.ly/QHSupport >> Chat with Us
Regards,
Quick Heal shows ‘Protection is out of date’
On clicking ‘Update Now’ it shows ‘The version of Internet Security you have is up-to-date’
Virus database 16 July 2015
RIZE ALPHA ONE MALL
RIZE – ALPHA ONE MALL
Product Key: RT0105N16100618AB28A
License valid till: 10 July 2018
Installation Number: 8969-2318-8705
Thanks.
Mobile: 9825021167
Hi,
Our Support Team can help you solve this issue:
1. You can submit your query at https://bit.ly/Askus. The Team will get back to you with a solution.
2. You can also contact them at 0-927-22-33-000.
3. Alternatively, you can chat with our engineers by visiting this link >> https://bit.ly/QHSupport >> Chat with Us
Regards,
The update definition file is corrupt.
aborting the update process ?
Hi Sankar,
Our Support Team can help you solve this issue:
1. You can submit your query at https://bit.ly/Askus. The Team will get back to you with a solution.
2. You can also contact them at 0-927-22-33-000.
3. Alternatively, you can chat with our engineers by visiting this link >> https://bit.ly/QHSupport >> Chat with Us
Regards,
I am using net banking through chrome browser which is downloaded from play store. I have quick heal mobile anti virus so is that I am safe to continue net banking?
Hi Umar,
Yes, you can conduct net banking securely. However, as a safety measure, please ensure that you are on the right website.
Regards,
update problem was their from past four days.
Hi Sparsh,
Our Support Team can help you solve this issue:
1. You can submit your query at https://bit.ly/Askus. The Team will get back to you with a solution.
2. You can also contact them at 0-927-22-33-000.
3. Alternatively, you can chat with our engineers by visiting this link >> https://bit.ly/QHSupport >> Chat with Us
Regards,
YET ANOTHER CLEANER – YAC GOT LOADED IN MY SYSTEM AND WOULD NOT LET MY BROWSER OPEN UP , I CONTACTED MY ISP AND EVEN THEY WERE NOT ABLE TO LOCATE THE PROBLEM . IT WAS ACCIDENTALLY I DISCOVERED THAT AND THE SYSTEM CORRECTED ON DELETING THE SOFTWARE.
ALL THIS WITH QUICK HEAL TOTAL SECURITY ON
Hi Rajesh,
Our Support Team can help you solve this issue:
1. You can submit your query at https://bit.ly/Askus. The Team will get back to you with a solution.
2. You can also contact them at 0-927-22-33-000.
3. Alternatively, you can chat with our engineers by visiting this link >> https://bit.ly/QHSupport >> Chat with Us
Regards,
System is secure
System is being actively protected
No action required
Hey,
I want to format my computer but my quick heal is license version so when i will format my pc and re-install quick heal and re-type my serial keys whether it will work or not ??
Hi Ravi,
Yes, you can reinstall your Quick Heal using the same serial key.
Regards,
i am using quick heal and purchased after reading review on https://www.techaj.com .
Thanks to quick heal because my pc is safe. total security is best suite. thanks technology assummed