VirTool Injector – Esoteric Bot

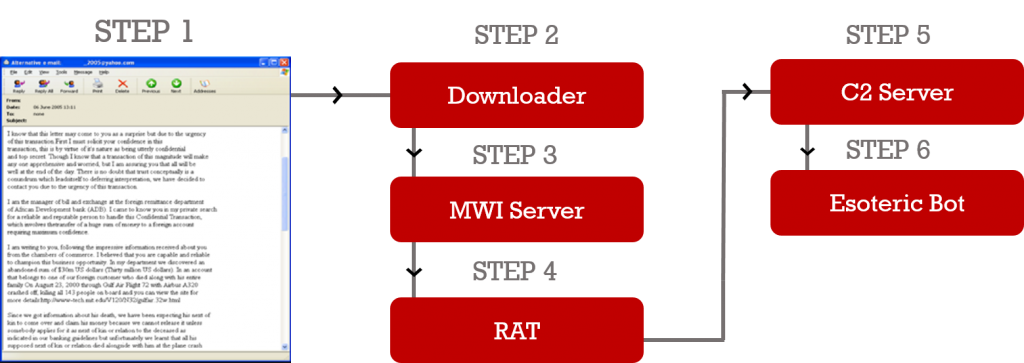
Quick Heal Threat Research Labs is tracking a malware known as Esoteric Bot. This blog post provides a technical overview into the behavior, work flow, and infection vector of this malware. It also discusses its preventive measures that must be taken by users. Infection Vector of Esoteric Bot Spam emails or drive-by-downloads are the common techniques used to spread this malware. The targeted victim receives a spam email with a malicious attachment. This attachment is built with Microsoft Word Intruder (MWI) which downloads the payload. Figure 1 describes the step-wise infection mechanism of this bot.
From its connected server, the malware downloads a RAT (Remote Access Trojan) tool. This tool is designed to steal the victim’s personal and confidential information, and provide the infected machine’s access to the remote attacker. A RAT can also download other executable files from its Command and Control server, which, in this case is the Esoteric bot. About Microsoft Word Intruder (MWI) Server Microsoft Word Intruder (MWI) is an exploit kit designed to easily build malicious Word files that can exploit various vulnerabilities in Microsoft Office. A document generated with the MWI exploit kit calls back to the server to download its payload, and it contains one or all of the following exploits:
- CVE-2010-3333
- CVE-2012-0158
- CVE-2013-3906
- CVE-2014-1761
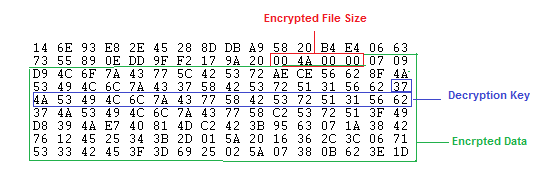
About Microsoft Word Intruder (MWI) Stat Server: Along with the malware builder, it also provides a Web-based console for tracking infections and can run multiple campaigns. The payload keeps its communication with its C2 server to keep a track of the infected systems. Understanding the Esoteric Bot Until now, we have understood how the bot infiltrates a victim’s machine, the role of MWI and the kind of vulnerabilities it exploits. Now, we will look into the details of this bot. To evade detection by antivirus software, the Esoteric Bot is implemented using the .NET language. There is an increase in the usage of .NET based wrappers for distribution of the malware as it makes the malware analyst’s job more challenging to reverse the executables in the form of Microsoft Intermediate Language (MSIL). This payload is kept in an encrypted form with custom encryption in resource of MSIL file in most of the cases. Figure 2 shows the structure of .NET resource and it encryption mechanism.
The size of the key varies according to different files. The decryption operation used is byte XOR. Let’s have a look at the decryption routine: KeyBuffer [] = { 0x37, 0x4A, 0x53, 0x49, 0x4C, 0x6C, 0x7A, 0x43, 0x37, 0x58, 0x42, 0x53, 0x72, 0x51, 0x31, 0x56, 0x62, 0x37}; for (i = 0; i < sizeof(EncrDataBuffer); i++) { EncrDataBuffer[i] = EncrDataBuffer[i] ^ KeyBuffer[i % KeyLen]; } After the first level of decryption, the resultant file is again an MSIL executable protected with .NET Obfuscator ConfuserEx v0.5.0-10-g6ebee. It contains a single resource named “Param”. Payload Delivery Flow
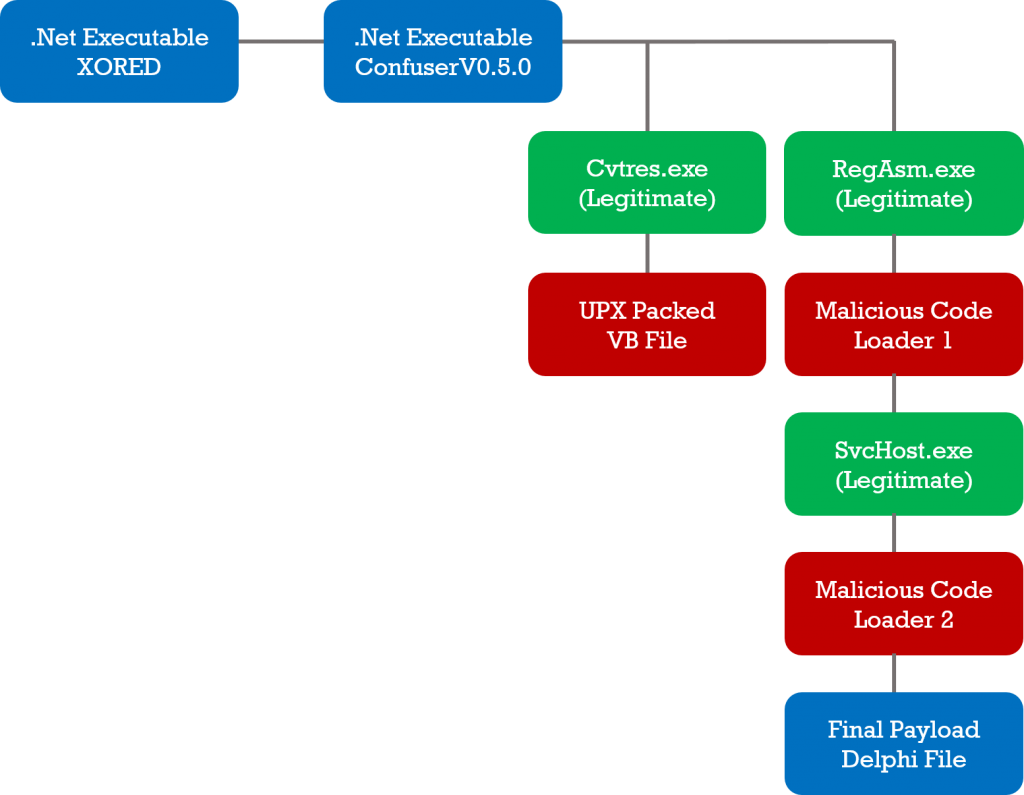
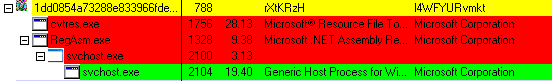
Figure 3 depicts the execution of the Esoteric bot in different stages. It uses the Process Hollowing technique to hide the presence of malicious processes in the infected system. It starts seemingly innocent or as a system process in suspended state. It then unmaps the image of legitimate processes, writes its own malicious code and then resumes execution of a newly mapped image. Esoteric bot uses CVTRES.EXE and REGASM.EXE which are part of Microsoft .NET Framework found at: C:WINDOWSMicrosoft.NETFrameworkv2.0.50727 Esoteric bot keeps multiple objects in its resource. All these objects are encrypted by custom logic. Once these objects are decrypted, they are launched with these legitimate processes. As figure 3 exhibits, CVTRES.EXE is launched with a UPX packed file, and REGASM.EXE is launched with a Borland Delphi file. The code injected in REGASM.EXE has another level of decryption and the decrypted code is then injected into svchost.exe. This decrypted code communicates with the C2 server and downloads plugins of the Esoteric bot. Figure 4 shows the process injection tree.
Inspecting the Final Payload
- First, it iterates through every process and searches for its parent process. If the parent process is other than svchost.exe or explorer.exe, then it terminates. It also checks for the privilege of the user account. This information is required while communicating with the bot server.
- It then creates a copy of the malware to C:Documents and SettingsAdministratorLocal SettingsApplication DataMicrosoftWindows<random_name.exe> and
%temp%<random_name.tmp>
- The values assigned to this key is the original malicious file of Esoteric bot. It uses RegSetValuesExA() for storing PE file in registry. The following keys are added. Before adding any values to these keys, it will query it first. Only if it fails, it proceeds, else it skips this step.
HKEY_CURRENT_USERSoftwareGoogleUpdatenetworksecure� HKEY_CURRENT_USERSoftwareGoogleUpdatenetworksecure1 HKEY_CURRENT_USERSoftwareGoogleUpdatenetworksecure2 HKEY_CURRENT_USERSoftwareGoogleUpdatenetworksecure3 HKEY_CURRENT_USERSoftwareGoogleUpdatenetworksecure4
- Next, it modifies the run entry. The value passed to it is a copy of the Esoteric bot, dropped as Application DataMicrosoftWindows<random_name.exe>
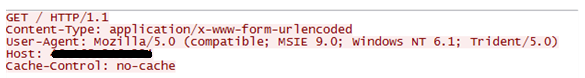
HKEY_CURRENT_USERSoftwareMicrosoftWindowsCurrentVersionRunBhUIUWh0tNOv3A0zkA Network Activity The bot has communication information and C2 server address in an encoded form. It tries to connect to the same C2 server every 20 seconds when the connection fails.
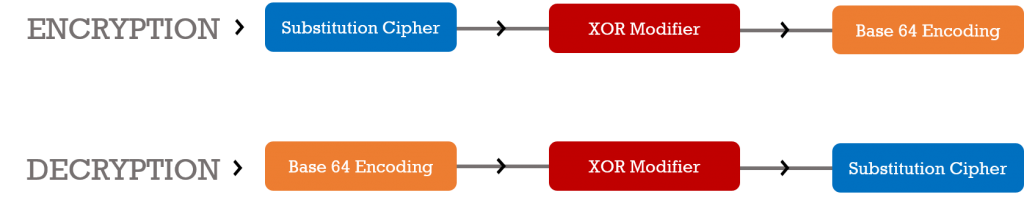
If a valid response is received, it creates a URL with information which includes the infected machines’ Operating System version, and access privilege in the following format: <local>-<os_version>-<random-number> The random number used to generate the URL is stored in the registry. The malware selects the random number from these bytes. Before downloading further plugins, it verifies if the plugin for the Esoteric bot is installed or not. To verify this, it will query the registry key which gets updated in an earlier stage of the infection. HKEY_CURRENT_USERSoftwareAdobeAdobe Acrobatin Once the URL is formed with local information, it is encoded using three steps. This algorithm is also used to encode/decode other strings in memory. Let’s have a look at this algorithm. First Step: Substitution Cipher By using a custom substitution routine, URLs are encoded. This routine substitute a URL’s characters using a hard-coded lookup table. Different lookup tables are used for encoding and decoding. The lookup table used for the decoding phase is 512 bytes long. Second Step: XOR Encryption The substituted data passed to the XOR Encryptor with four different values based on the type of data to encrypt, is as follows:
| Value | Type of Data |
| 0xBB8 | Windows API |
| 0x264D | URL to send |
| 0x1918 | Receive data from C2 server |
| 0x2328 | Plugin names in registry |
Third Step: Base 64 Encoding The XOR data is then passed to Base64 encoder. By using these three steps, the malware can perform an encryption/decryption of all the data that is to be sent over the network. Figure 6 exhibits the step-wise operations.
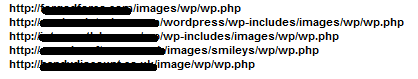
Downloading the plugins At this stage, the bot is ready to download its plugins like Pony malware, MBR Wiper, etc. It connects to its server and writes plugins below the following registry key. The first plugin that gets downloaded is MBR wiper. HKEY_CURRENT_USERSoftwareGoogleUpdatenetworksecure Pony Stealer Another plugin which it downloads is a recent version of the Pony Stealer malware – designed to steal user credentials and even Bitcoin wallets. It has a list of domain names to which the stolen information is sent, along with the login information for these domain.
Some passwords that we found in memory include: 123456, password, phpbb, qwerty, 12345, jesus, 12345678, 1234, abc123, letmein, test, love, password1, hello, monkey, Dragon, trustno1, 111111, iloveyou, 1234567, shadow, 123456789, Sunshine, and master. VNC Plugin It also downloads a Virtual Network Computing (VNC) plugin which provides attackers with keyloggers and hide desktop functionality. By running a VNC module, it is possible to watch the victim without getting noticed. VNC plugin is stored in an encoded format inside the following registry key. The above described algorithm is used to decode it. Before injecting the VNC plugin, the malware searches for some legitimate applications that provide the facility of VNC and if any running processes are found, the malware kills them. Some applications that provide VNC facility are listed below.
- RealVNC
- UltraVNC
- TightVNC
It checks if any of the reverse engineering tools installed on the victim’s machine is from the below list; if found, it terminates them:
- vmware
- snort
- wireshark.exe
- regmon.exe
- filemon.exe
- procmon.exe
- VBoxService.exe
- VMwareTray.exe
- VMwareService.exe
- VMwareUser.exe
- procexp.exe
- Tcpview.exe
- cff.exe
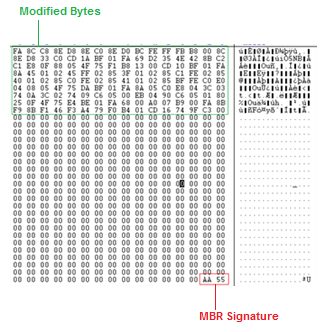
MBR Wiper Once the plugin is downloaded, it is loaded in SvcHost.exe by using Process Hollowing. Once executed, activities are listed in sequence, which is as follows:
- First it will create a file \\.\PhysicalDriveN.
- Next it will write 512 bytes
- Exits the process
After that, the parent process removes any bookmarks of the malware from the registry, and restarts the machine via ExitWindowsEx(). Prevention Esoteric bot targets vulnerabilities in Microsoft Office using MWI. To prevent an infected Word document from breaching a system, latest security patches must be applied to Microsoft Office. Equally important is to be aware of spam emails and not clicking links or opening attachments from unwanted, unsolicited, and unknown senders. ACKNOWLEDGMENT Subject Matter Expert: Swapnil Patil, Quick Heal Threat Research & Response Team.
1 Comment
Nice report…!
Great Analysis!