How to Prevent Ransomware From Locking Your PC
The Quick Heal Threat Research Lab has been detecting increased numbers of ransomware infections over the last few weeks. We have recently reported on the notorious Dridex ransomware. These incidents depict a clear trend that malware authors are steadily shifting to serious money making ransomware variants.
The rise in these ransomware variant detections can be attributed to the following primary reasons:
- Ransomware has proven itself as a highly effective money extortion mechanism over the last year.
- Ransomware has become much easier to develop due to the availability of source code and the emergence of ‘Ransomware-as-a-service’ products in the black market.
- Ransomware is increasingly being used along with other successful and penetrative malware propagation techniques such as spam campaigns, ‘Malvertising’ and ‘Social Engineering’.
- Ransomware has become efficient due to the presence of Bitcoins, a digital currency that enables cybercriminals to collect money anonymously.
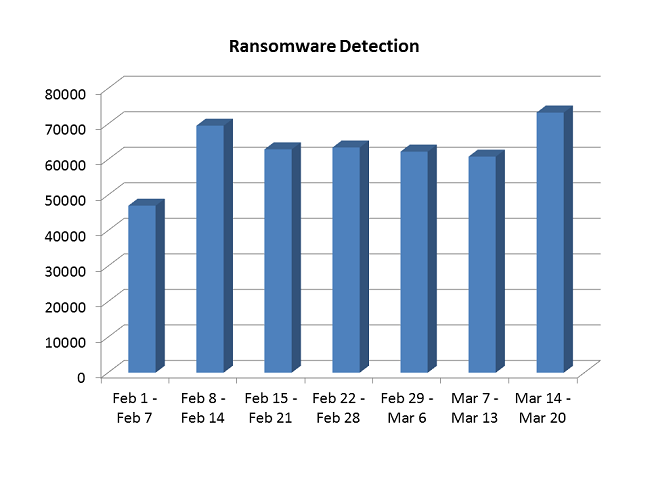
Stats for Ransomware Detection by Quick Heal
This graph shows the number of ransomware detections by Quick Heal for the 7 weeks starting from February 1st, 2016. In this time period, our lab has detected nearly 450,000 ransomware samples, which work out to approximately 9,000 ransomware detections every single day. These figures present a considerable rise in the ransomware detections that we have seen in the past, and they highlight the growing threat of ransomware to businesses and individual users.
There are a few foolproof precautions that need to be undertaken to prevent ransomware variants from infiltrating and locking your machine. These safety guidelines are even more relevant for enterprises and small business owners who are often the most sought after victims of ransomware authors.
1. Backup your data often and in different ways
When it comes to data security, the first step is data classification. It is essential for data owners to segregate their data into crucial, moderate or dispensable categories and then devise ways to secure their most sensitive information. We recommend the 3-2-1 rule – maintain 3 different copies of data, in 2 different formats, with 1 format available offline.
2. Update your OS and other applications & utilities
Malware developers typically exploit vulnerabilities in applications and the OS to breach system security. To prevent incidences it is highly recommended to automatically download OS updates, and apply regular security patches for other applications on the system. Commonly targeted applications are Java, Adobe Acrobat Reader, Adobe Flash Player, MS Office and web browsers such as Google Chrome, Mozilla Firefox, Internet Explorer and more.
3. Be cautious of suspicious emails and attachments
Spam emails have become one of the most effective ways for ransomware to enter vulnerable systems. Through social engineering techniques or by disguising emails to appear as authentic ones, attackers cause victims to click on fraudulent links or download malicious attachments. When it comes to email security, we suggest the following security measures:
- Always check the email senders information
- Always verify the content of the email properly
- Never click on the links embedded within suspicious emails
- Never open or execute attachments received from unknown senders
Some More Ransomware Prevention Techniques
- Personalize spam settings for your email inbox and your installed security solution.
- Use the native Windows functionality of ‘Show File Extensions’. This shows the extensions of unknown files before opening them.
- In case of breaches or infections, immediately disconnect the Internet connection.
- Keep the Windows Firewall switched on at all times and regularly monitor its settings.
- Enable your installed security software to scan compressed and archived files when they enter the system.
- Turn off AutoPlay for USB devices, so that they do not immediately open the files within them.
- Consider installing an add-on which blocks automatic pop-ups on your browser.
Recently, ransomware infections have begun spreading via JavaScript codes on websites as well. So there are multiple avenues through which ransomware can be delivered into vulnerable systems. Quick Heal defends against the latest malware samples with generic and heuristics-based detections that are discovered through our global virus signature database on a daily basis. Moreover, Quick Heal security products also provide multiple lines of defense such as Virus Protection, Email Protection, DNAScan and Advanced Behavior Detection System for complete system security.


134 Comments
Last week i upgraded my QHTS Ver.16 to 17..
Can QHTS 17 detect ransomware?? Because i dont find about antiransomware.exe on my windows 8 task manager service….please reply
Hi Pallab,
Yes, the Quick Heal software on your device is actively blocking ransomware on your machine. However, you must also take all the necessary precautions to prevent ransomware infections.
Regards.
nice update.such infomations are very important.
sir, meri drive lagbhag aadhi khali hai phir bhi 0 space dikha raha hai or ajeeb ajeeb tarah ki file dikh rahi hai main kya karu mera data bahut keem ti hai because meri photography ka kaam hai sabhi data important hai plz solution bataiye. please.
Hi Salman,
May we request you to contact our technical support team. They will help you resolve this issue as soon as possible. You can reach them here – https://www.quickheal.co.in/submitticket.
Regards.
i like quick heil
These ways of protection are not enough. Can this ransomeware be completely removed from machine by rebooting, and can be repaired by Quick heal total security? Or you have any other option.
Hi Avik,
Ransomware variants are constantly changing and there is no software that can completely block all kinds of ransomware before they are even created. So all security products are reactive in nature to some extent. However, if users undertake some of the precautions mentioned here and also use an effective security solution, then the chances of avoiding ransomware are high. So it is best to remain proactive and alert when it comes to security and not depend on a security solution only.
Best regards.
data transfer is lo please help
Hi Ajay,
May we request you to contact our technical support team. They will help you resolve this issue as soon as possible. You can reach them here – https://www.quickheal.co.in/submitticket.
Regards.
Yes, I trust Quick Heal but I am using Quick Heal Internet Security version 16.00 (9.0.0.54). When I upgrade to it’s latest version version 17.00 (10.0.0.6) it consume more RAM & slow down my PC, increase startup & shutdown time. That’ss why I am using version 16.00 (9.0.0.54) again. Also When start LIVE CHAT on your website, I did’nt received Chat transcript but it show Mail has been sent successfully.
Hi Anirban,
May we request you to contact our technical support team. They will help you resolve this issue as soon as possible. You can reach them here – https://www.quickheal.co.in/submitticket.
Regards.
I have been purchased on Amazon Quick Heal Total Security-2PCs 1 Year (CD)X000F9YAE1 vide your cash memo No PB-STA-137231171-22172 dated 21 Mar 2016.
Please keep update Quick Heal Total Security on my PC till updating the CD on my PC please.
Thanking you
Hi Babaji,
May we request you to contact our technical support team. They will help you resolve this issue as soon as possible. You can reach them here – https://www.quickheal.co.in/submitticket.
Regards.
Yes I trust in Quick Heal
good
its good
Thumbs up to Quick Heal, I will henceforth start introducing and recommending Quick Heal to my friends.
Please advise whether we can have Windows Firewall on even when Quickheal antivirus security is running.
Hi Col. Laddha,
Yes you definitely can have Windows Firewall ON as well. This is an in-built feature in Microsoft operating systems, and it is an added security layer that should certainly be used in addition to any security software on your device.
Best regards.
like
YES
sir i am not able to update my pc
Hi Vivek,
May we request you to contact our technical support team. They will help you resolve this issue as soon as possible. You can reach them here – https://www.quickheal.co.in/submitticket.
Regards.
Verry useful app
wow
ITRUST QUICK HEAL SOFFTWEAR VERY GOOD ANTY VIRUS
my pc is very slow runing
Hi BK Mandal,
May we request you to contact our technical support team. They will help you resolve this issue as soon as possible. You can reach them here – https://www.quickheal.co.in/submitticket.
Regards.
sir, i am a layman . so it is my request to u to inform us in simple way —what to do n not to.
i like this
My PC has slow down after instalation of gardian antivirus from quickheal , Why?
Hi Azad,
May we request you to contact our technical support team. They will help you resolve this issue as soon as possible. You can reach them here – https://www.quickheal.co.in/submitticket.
Regards.
QH isn’t as effective as MS Security Essentials in detecting and killing ransom virus. Org. like QH should find soln. to unlock files affected by ransom as a service to its reg. users.
QH updating is fictional and not practical or real, for QH cannot remove or fight with ..ware effectively and after each update my PC gets slow in operation.
Hi i am use quickheal.this is very good choise for my PC.he protect my PC always.this is good.
good idea and steps
i agree
I WANT TO UPTODATE MY SYSTEM BUT GUARDIAN ANTIVIROUS DOES NOT SUPPORT IT WHAT DID I DO
Hi Amrit,
May we request you to contact our technical support team. They will help you resolve this issue as soon as possible. You can reach them here – https://www.quickheal.co.in/submitticket.
Regards.
I didnt update my products, there have show that “error 1001”. I tried so many times but every time show the same messege, please solve my problem
Regards
Koushik
Hi Koushik,
May we request you to contact our technical support team. They will help you resolve this issue as soon as possible. You can reach them here – https://www.quickheal.co.in/submitticket.
Regards.
Is QH update necessary every-time or old QH version can prevent virus if we are not connecting the internet.
Hi Chetan,
Updates are important because the global virus database gets updated in real-time. Every day there are thousands of new malwares that are created and detected and our database is accordingly updated. So if you miss out on some updates it is essential to get them soon, as your machine may then be infected by a sample that has not been updated in your software.
Regards.
How can update it.
Hi Yusuf,
May we request you to contact our technical support team. They will help you resolve this issue as soon as possible. You can reach them here – https://www.quickheal.co.in/submitticket.
Regards.
good
I am use in Quick Heal and good working
Quick Heal Totol Security is a best anti virus 100%Original
It is udefull to protect my both device mobile & computer. I want more help from this anti-virus.
good
This is useless product when comes to Locky Ransome malware virus which did not even prompt for malware when our server was hacker which had 15years data. We have been using this product for 7-8 years with regular updates and timely activation done for 3yrs. There customer support is never reachable as we need to wait for 50-60 mins but no one will come on line. If any tech comes online they simply do not understand the issue and say we are helpless. THIS IS USELESS PRODUCT, NO SUPPORT, WASTE OF MONEY. THEY ARE THE BIGEST HACKERS WHITHOUT PROVDING SUPPORT.
Hi Bharathi,
We understand your displeasure as a customer. There could be more than one reason behind this incident. We have shared your concern with the team and they will get back to you soon.
Regards,
pls how can you help me with my pc and i need to upgrade my qiuck heal anti-virus
Hi Moses,
Which Quick Heal product are you using?
Regards,
This has given me a good start on learning to fight and prevent Ransomware infection. Thanks!
I’m impressed with what I have seen and read so far.
Best security…….
Sir, please also tell about how to destroy ransomware file. I mean either to delete the file or my quick heal will repair it. Please answer
Hi Vineet,
Our support engineers would gladly help you with this issue. Please visit https://bit.ly/QHChat to chat with us online. You can also raise a ticket at https://bit.ly/Askus and we will get back to you at the earliest.
Regards,
virus cleaner my pc
how to start the antivirous
Hi Aman,
To start Quick Heal, go to Start > All Programs > Quick Heal
Regards,
QUICK HEAL TOTAL SECURITY
windows 10 not firewall on
Hi Omprakash,
Please explain your query in detail so that we can assist you.
Regards,
Thanks a lot for this important message. Keep it up God Bless.
How i mainten my device from mailware .
Hi,
Please read our post below to know how to keep your device safe from malware and other threats:
https://blogarchive.quickheal.com/wp/45-killer-security-tips-to-follow-on-computer-security-day/
Regards,
sie mera antivirus update nhi ho pa reha hai
Hi,
Thanks for writing in. Our support engineers would gladly help you with this issue. Please visit https://bit.ly/QHChat to chat with us online. You can also raise a ticket at https://bit.ly/Askus and we will get back to you at the earliest.
Regards,
can the net secure perceive itself and prevent it. why blame the customer for having not personally set it
Hi Jatindraprasad,
Thanks for writing in. Our support engineers would be able to answer your query in detail. Please visit https://bit.ly/QHChat to chat with us online. You can also raise a ticket at https://bit.ly/Askus and we will get back to you at the earliest.
Regards,
Respected QuickHeal Team,
I have encountered the same Virus Encryption Problem with RSA-4096 and my all documents are corrupted. Anyhow, I removed the Virus completely by Quick Heal Pro, so there are no viruses now but my files are still encrypted. Could you suggest me how to decrypt the files? I tried Recuva, Shadow Explorer but nothing helped me. It is very urgent for me.
Hi,
Thanks for writing in. Unfortunately, files encrypted by a Ransomware are almost impossible to get back or decrypt without paying to the hacker. It also depends on the grade of encryption used. However, we’d request you to have a word with our support team; they would like to analyze the issue. Please visit https://bit.ly/QHChat to chat with us online. You can also raise a ticket at https://bit.ly/Askus and we will get back to you at the earliest.
Regards,
QH is really working hard to safe guard my pc
its not work properly.whenever antivirus is not detect the virus and my lappy is not protected
Hi Khushboo,
Thanks for writing in. Our support engineers would gladly help you with this issue. Please visit https://bit.ly/QHChat to chat with us online. You can also raise a ticket at https://bit.ly/Askus and we will get back to you at the earliest.
Regards,
after disabling secure boot quick heal now installed , it will be no problem after disable this further ? if any please mention
Hi Pankaj,
Thanks for writing in. Our support engineers would gladly help you with this issue. Please visit https://bit.ly/QHChat to chat with us online. You can also raise a ticket at https://bit.ly/Askus and we will get back to you at the earliest.
Regards,
yadav.pal30@gmail.com
im forget my activation code
please provide my code??????
Hi Pal,
Thanks for writing in. Our support engineers would gladly help you with this issue. Please visit https://bit.ly/QHChat to chat with us online. You can also raise a ticket at https://bit.ly/Askus and we will get back to you at the earliest.
Regards,
it is essential for me
hi , i am renewed quick heal software on my pc on 04/04/2016 but it has been frequently show that product key cannot be renewed .the provide product key is renewed within 10 days. tell me sir, how can i solve this problem ?
Hi Jagannath,
Thanks for writing in. Our support engineers would gladly help you with this issue. Please visit https://bit.ly/QHChat to chat with us online. You can also raise a ticket at https://bit.ly/Askus and we will get back to you at the earliest.
Regards,
OK
nice
sir i want to suport from quickheal centre.plz contact own my no 906044676
Hi,
Thanks for writing in. Our support engineers would gladly help you with this issue. Please visit https://bit.ly/QHChat to chat with us online. You can also raise a ticket at https://bit.ly/Askus and we will get back to you at the earliest.
Regards,
supar
Dear ,
How i use it on my Laptop & Mobile device same time?
Hi Rabindra,
One Quick Heal product can be used on one system at one time. Please let us know if you have any queries.
Regards,
Its not a new problem i have faced it in 2010 when i install a suspicious netbooster and at that time quickheal total security also failed to save my computer from that infection at last i went for windows format process to get rid of that ransomware.
Hi Dhananjay,
We are regretful to learn about your unpleasant experience. We’d like to assure you that our products are more capable and advanced than before when it comes to countering ransomware attacks. Do let us know if you have any queries.
Regards,
Some day before updates were workingand after that stoped.
Hi Ganesh,
Thanks for writing in. Our support engineers would gladly help you with this issue. Please visit https://bit.ly/QHChat to chat with us online. You can also raise a ticket at https://bit.ly/Askus and we will get back to you at the earliest.
Regards,
Nice
Hello quickheal
Hello sir
Maine apne phone ko kingroot app se root kiya huaa hai. Nd phobe ko quic heal se scan karne per kingroot app ko threats show karta hai.
Then kya sach me kingroot app threats hai.
Hi Namit,
Thanks for writing in. Our support engineers would be able to assist you in this matter. Please visit https://bit.ly/QHChat to chat with us online. You can also raise a ticket at https://bit.ly/Askus and we will get back to you at the earliest.
Regards,
uptudate atumatic
update nhi ho rha hai
Hi Narmdeshwar,
Thanks for writing in. Our support engineers would gladly help you with this issue. Please visit https://bit.ly/QHChat to chat with us online. You can also raise a ticket at https://bit.ly/Askus and we will get back to you at the earliest.
Regards,
Hi, Rahul,
I just share with you as per last week my all data is covered locky file and i have donload quick heal antivirus . After scan all file then detected locky file rensomware errors please suggest how to remove locky file virus so that we recover my ms word , excel files or PDF .
Thanks
Hi Sanjay,
Thanks for writing in. Our support engineers would gladly help you with this issue. Please visit https://bit.ly/QHChat to chat with us online. You can also raise a ticket at https://bit.ly/Askus and we will get back to you at the earliest.
Regards,
Team Quick Heal
viras activet in mameri
Hi Rajesh,
Thanks for writing in. Our support engineers would gladly help you with this issue. Please visit https://bit.ly/QHChat to chat with us online. You can also raise a ticket at https://bit.ly/Askus and we will get back to you at the earliest.
Regards,
nsice
Maybe in my phone have a virus so I can’t clear cool my app allow data or android so can u give me something idea please
Hi,
Thanks for writing in. Our support engineers would gladly help you with this issue. Please visit https://bit.ly/QHChat to chat with us online. You can also raise a ticket at https://bit.ly/Askus and we will get back to you at the earliest.
Regards,
pleas prevent my ransomewera from looking your pc
Sir, I have quick heal pro installed on my laptop, yet it recently got infected by a ransomware, which encrypted all my office and pdf files. Now I am not able to access those files as their file type has been changed to CRYPT.
I formatted my laptop last month and unfortunately did not take a backup since then.
Tried to recover files via system storage but it didn’t work. I would highly appreciate it if you could suggest me with some solution which could help make those files usable again.
Regards,
Hi Kapil,
Thanks for writing in. Our support engineers would gladly help you with this issue. Please visit https://bit.ly/QHChat to chat with us online. You can also raise a ticket at https://bit.ly/Askus and we will get back to you at the earliest.
Regards,
Dear sir..I like these antivirus..
Hi Rahul,
All files from my PC gone corrupt coz of ransomeware, pls tell me how can i get those files back
Hi Saurabh, Thanks for writing in. Our support engineers would gladly help you with this issue. Please visit https://bit.ly/QHChat to chat with us online. You can also raise a ticket at https://bit.ly/Askus and we will get back to you at the earliest.
Regards,
Real hero for pc
Nice one
Are users of Quickheal anti-virus protected from the attack of Ransomware. Please provide some tips for us to check whether there is any chance of breach of security and to take steps to overcome the same. Eg., those who have adopted Quickheal anti-virus may not have the anti-malware and it may affect the PC.
Hi Pauline,
Yes, Quick Heal users are protected from Ransomware attacks. You can follow the tips mentioned in this post.
Regards,
frequently my system is damaged by some antivirus. Why is it software is not detect and remove those wireses?
Hi!
Thanks for writing in. Our support engineers would gladly help you with this issue. Please visit https://bit.ly/QHChat to chat with us online. You can also raise a ticket at https://bit.ly/Askus and we will get back to you at the earliest.
Regards,
Sir, My product key is invalied sow, kry is
BU8CE4GE1R2720812B10. kindly quick active from you .
Thanks
cell- 09401306058
Hi Babul,
We’ve shared your concern with our team. They will get in touch with you shortly.
Regards,
i just want to instal google
bad service quickheal antivirus
dear sar palls anter vares key
Hi,
If you have lost your product key, please click on the link below:
http://www.quickheal.com/lost
Regards,
How to remove Malware from this PC ?
Many time scaned but it does’t go. The Malware name is $RECYCLE.BIN and System volume Information.
Hi Tika,
Thanks for writing in. Our support engineers would gladly help you with this issue. ou can also raise a ticket at https://bit.ly/Askus and we will get back to you at the earliest.
Regards,
bakwas antivirus, only useless, 1000 gb data has been lost, make av more effective.
Hi,
Thanks for writing in. We have shared your feedback with our team so that they can look into the matter. In the meantime, you can visit https://bit.ly/QHChat to chat with us online; our support engineers would gladly help you with any issue that you might be facing.
Regards,
I am using quick heal
mast