Beware of the Hidden Threats of Corrupted Software Files!
From a minimal calendar app, to a jazzy media player or a popular PC game, we all love downloading freebies from the Internet. And this common interest of ours is just well too known by attackers.

Downloadable files on the Internet are one of the most common mediums used by attackers to transmit viruses and malware. An attacker can insert a malicious code into a file which could be a word doc, image, or any other file which is normally considered to be innocuous. Once the attacker has compromised a file, they may distribute it via an email, websites, torrent link, social media channels, etc. The type of malicious code launched by the attacker depends on the end result they want to achieve. For instance, if a hacker is after your personal information like usernames, passwords, bank account information, etc., then they would trick you into downloading a spyware-infected file on your computer. Once inside the system, the spyware will collect all possible information about you and pass it on the attacker.
So, what common problems can corrupted software cause?
Depending on the malicious code the software has been corrupted with, the problems may vary. However, most malicious codes are designed to perform one or more of the following functions:
- Slowing down your computer. Infected machines may start freezing frequently, and become unresponsive.
- Corrupting the core files of the infected computer.
- Stealing data stored in the computer, and information related to the user’s Internet activities.
- Allowing other viruses and malware to gain entry into the system.
- Giving partial or full access of the computer to the attacker.
- Using the infected computer as a bot to attack other victims.
- Redirecting users to fake websites and stealing their login ID and passwords, even financial details.
- Causing the computer to use too much memory and resources than normally required.
- Causing random files to go missing without your knowledge.
Safety Tips
1. The most important measure to take is to be extremely choosy about free software available on the Internet. Before downloading any type of application, ensure that you
- Do a quick research on the software, its user reviews and ratings.
- Ensure that the site you are downloading the software from is well-known and trusted.
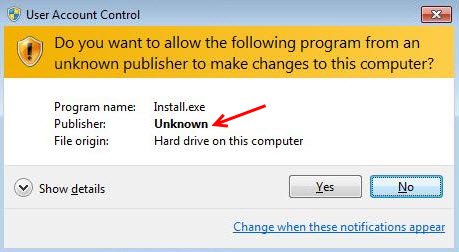
2. While installing the software, check if it’s from a verified publisher. If it’s not, then do not proceed.
3. Install an antivirus software in your PC. When you are going for it, ensure that the software offers protection against unsafe websites, infected files downloaded online, emails that carry infected links or attachments, and all types of virus and malware infections.
4. Be skeptical about unwanted or unknown emails. Even if the sender seems familiar, exercise caution if the email talks about something which you were not expecting or have no prior knowledge about.
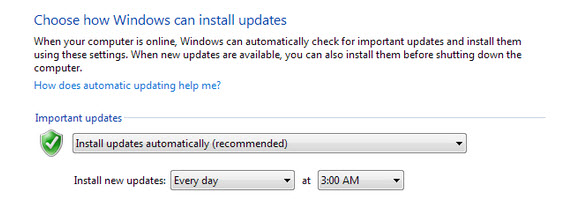
5. Apply software updates whenever available. This is more important with Windows security updates that are released periodically. Doing so will fix any security holes that might be present in your system. Security holes are a hacker’s prime method to get their malicious code to execute on a victim’s machine. It is strongly recommended to always keep the Windows Automatic Updates ON.
Related information
• Why are Software Updates so Important for your Security
43 Comments
so good
use ful informastion.
I HAVE VIRUS IN MY PC WHEN I STARTED PC THAN HE ACTIVATE MESSAGE DISPALY ON SCREEN THAT tirsaeme has encountered a problem and needs to close. We are sorry for the inconvenience.
TELL MICROSOFT ABOUT THIS PROBLEM
If you’re using an original version of Windows then the mentioned message should also display an error code which the system is encountering with. Just Google for that code & you can be able to know the possible causes behind the problem. There can be various reasons behind this kind of problem including virus infection.
You can also try the Quick Heal Emergency disc if you have one, proving that it’s created with the latest virus signature database. Boot from the disc & it’ll detect & repair any boot time infection if there is any.
You can also try to format C drive & go for a clean install of Windows.
A very informative information. Glad that you are spreading this type of information. Will hope in future, you will also like to such precious information with the users.
excellent information for users they working always online.
useful
So Good
Am very thankful to quickheal 4 awaring everyone against malwares and viruses…. Gr8 job!!!
an out of context question.
what is the purpose of CAPTCHA.
can you please send a copy of reply to my mail.
Hello Dr. Sachindra Kanoria,
A CAPTCHA (an acronym for “Completely Automated Public Turing test to tell Computers and Humans Apart”) is a type of challenge-response test used in computing to determine whether or not the user is human. This tool is used to block spammers and bots that try to automatically harvest email addresses or try to automatically sign up for or make use of Web sites, blogs or forums.
Regards,
good
But in you andriod mobile antivirus total security there is no applock service how to safe handset app
play store
Hi Mahesh,
You can check out our newly launched app called Fonetastic. It offers App Lock, Batter booster, and other cool features. Check out the free and pro versions here: https://bit.ly/FonetasticPRO | https://bit.ly/FonetasticFREE
Regards,
hi
i have a version 15.0 of quick heal and an update recently poped up to update my version to 16.0. It said it will reboot my present files and save the files on the new version.
Is this true or a fake!! Does the site for quick heal start with https or http?? Please guide me!!
Hi Nilesh,
If you have receive the prompt from your Quick Heal software, then it is a genuine message. However, in case of any doubt, our support team can help you with this:
1. Kindly submit your query at https://bit.ly/Askus
2. You can also contact them at 0-927-22-33-000
3. Alternatively, you can chat with our engineers by visiting https://bit.ly/QHSupport
Also, Quick Heal’s website’s URL begins with http. However, it does not mean that it is not safe.
Regards,
Following warning message from Quick Heal Antivirus Pro which keeps popping up every now and then
“Website you are visiting may be harmful
Website:- nersojooker.com/ads.php
Access to Website is blocked for your protection”
Please guide me as to how to get rid of this virus which has infected my PC.
Hi Ramesh,
The message that you have received is nothing but an update from Quick Heal that it has blocked this particular website. So, there is nothing to worry about; your PC is safe.
Regards,
HI RAJIB SINGHA,
I TOO HAD A SAME PROBLEM LIKE MR.RAMESH.I AM HAPPY FROM YOUR REPLY. BUT THE NOTIFICATION IS COMING OFTEN FROM QUICK HEAL.CAN YOU SAY, HOW TO STOP THIS NOTIFICATION?..
Hi Kavin,
If you wish to stop Quick Heal from sending you notifications, then follow the steps mentioned below:
1. One your Taskbar, find the Quick Heal icon.
2. Right click on it.
3. Select Silent Mode.
Regards,
quick heal antivirus pro product keys 9sb5-xxxxx-xxxxx-14310
Hi Tejurawani,
How may we assist you?
Regards,
so good
Thanks for this Information of Quick Heal & windows7 updates.
Thanks
Thanks Information for Quick Heal & Windows7 Updates. My PC is Very Good Speed.
Good
nice
soooooooooooo gooooood i very impress it
Very useful. I have been a victim of this problem. Thanks for sharing the information!
i have some problem for my pc my downloading is not safe pls help me
Hi Raj,
Why do you feel that your downloading is not safe? Could you explain to us a specific incident? We will gladly help you with a solution.
Regards,
Very good
my internet is so slow these days………. just not able to log on to facebook………. so difficult logging on to facebook……… today till now i tried to log twice during day but failed…….will try now…………lets see…….i do not download any software or games or application myself………. i only use this laptop………….kindly help…………thank you…………alpana kakati
Really useful..the tips given are very informative to protect the computer from
malicious or suspicious software….A great job done by Quick Heal team
Thanks…………….
Nice
Junk
Quick Heal is good.
Nice
Thanks
can someone help me with this? my pc crashes (shuts down) after about 30 minutes of use. sometimes it takes about 5 minutes to boot. I did a virus scan but it came up empty.
Hi Bill,
We request you to contact our technical support team. They will help you resolve this issue as soon as possible. You can reach them here – https://www.quickheal.co.in/submitticket.
Regards.