Instagram: What you need to know – Part 2
This post is in continuation with our previous post on Instagram and will discuss how you can control your privacy in the app.
In Instagram the key word is ‘public.’ Once an Instagram profile has been created, anyone can browse these online profiles and “follow” other Instagram users. Here comes the tricky part. How do you deal with privacy then?
First control your visibility. If you want only approved followers to view your profile:
- Go to your profile by tapping the far right address card icon.
- Tap the settings icon in the upper right corner.
- Apple iOS — Scroll to “Photos are private” and toggle the switch to ON to turn on privacy. Android — Tap on “Photo privacy” then tap the box to turn on privacy.
What happens then?
Once this is turned on, anyone who wants to see your photos, or followers and following lists, will have to send you a request that will appear in your News> You feed. You can then ignore or approve.
Once you turn your setting to private only approved followers can view your geolocation, photomaps and hastags. But there’s a glitch. If you share a private photo on social networking sites such as Facebook, Twitter, etc. the photo will be visible on that network and the permalink will be active. So anyone with access to that direct link/URL will be able to view the photo.
Now, if you have ever logged into your Instagram account using a web viewer, your images might pop-up in Google search. Third-party sites that are created using the Instagram API can access your profile and photos.
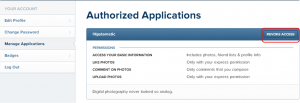
To revoke access to such sites, log into your accounts, select Edit Profile and choose Manage Applications.
It may take some time for these sites and Google to reindex and remove the images, even if you delete your account. You can find more information on how to remove photos here.
That said how do you control abusers and spammers on Instagram?
If you want to block someone, here’s how you do it:
To block or unblock someone:
- Go to their profile by tapping
 at the bottom of the app and searching for their name or username
at the bottom of the app and searching for their name or username - Tap
 in the upper-right corner of their profile
in the upper-right corner of their profile - Tap Block User or Unblock User
However, even if you block someone they might @mention you. This mention will appear in your newsfeed. To prevent it, you have to change your username.
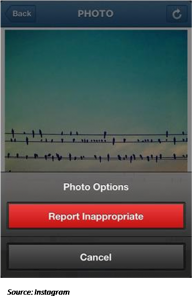
If you find a particular, photo to be abusive, profane or obscene you can tap the “…” below the photo you would like to report and then “Report Inappropriate.”
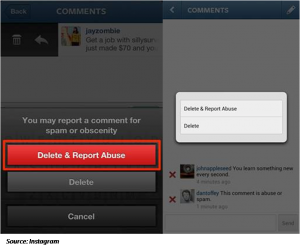
Similarly, you can report a comment in the following ways:
iOS devices:
- Tap the “comment” button below the photo, swipe your finger to the right over the comment you’d like to flag in order to reveal a trash can icon and a reply icon, then tap the trash icon and select “Delete & Report Abuse.”
Android devices:
- Tap the “comment” button below your photo, tap the pencil icon in the upper right, then tap the X icon next to the comment and select “Delete & Report Abuse.”
While flagging comments remember to flag only those that include: pornographic content, abuse that has escalated beyond a user dispute, spam, hate speech, personally identifiable information.
Additionally you can also report a particular user for spamming.
Visit their profile page, tap the button in the top right corner and tap “Report for Spam”.
As with any social platform, Instagram isn’t devoid of pros and cons. At the end it’s up to you to decide what information you want to expose and what you want to hold back and to what degree.
What you must also keep in mind here is that, if you have kids who use this app, there could still be people who can start following them using fake names and fake profile photos. Examples here include: making themselves look younger or to be of the opposite sex, or by appearing to be a classmate or peer.
For in depth understanding of how to address abuse on Instagram, please visit https://help.instagram.com/527320407282978/

6 Comments
What do you mean with applications? Do you mean apps or third parties websites?
Hi Magdala
This post and the one preceding it discusses about Instagram – the Photo and now Video sharing app.
If you could be a little more specific about your question and what aspect of the write-up that you are doubtful about, it would help us better in answering your query.
Regards
( REVOKE ACCESS ) instagrab app From Manage application on instagram Site , How can i add my apps instagrab Again to my Authorizing applications , What i should do ?? Can you help me Please
Hi Ateeq,
Apologies, but can you please explain the issue further? Do you mean that you accidentally categorized Instagram as an unauthorized application from the Instagram site itself? Please let us know more details so that we can assist you successfully.
Best regards.
Hi there,,
How I can hide comment which I mentioned to my girlfriend on love song in any account from my fellowre in Instagram,, because someone told my about my mentioned .
Hi Nasser,
We would advise to contact Instagram support service >> https://help.instagram.com/
Regards,