Why SMEs Need to get Serious about their IT Security?
What’s common between most small and medium enterprises? It is a false sense of IT security that they have. Most of these industries assume that they are too small to risk any cyber attack, and it is this very notion that cyber crooks take advantage of. This post explains why IT security of SMEs is no less important than that of the big players in the market.
Why do Most SMEs think they are Out of Cyber Crooks’ Radar?
We are too small to be spotted by hackers
Most SMEs conveniently put their IT security needs on the back burner, probably because of their low visibility in the market and mediocrity of the information/data they hold. And this very notion acts like the underbelly of such industries; they are seen as “easy and vulnerable” targets by cyber criminals.
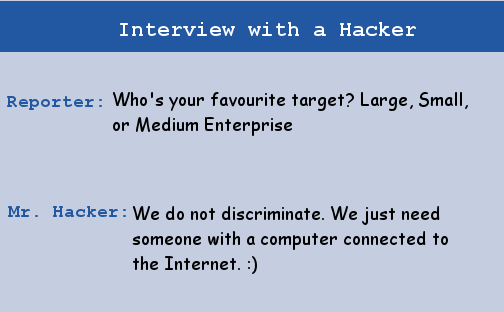
It is important to understand that cyber crooks do not have the following concerns in their toolbox:
1. How big a player is their target enterprise?
2. Who is running the enterprise?
3. How valuable is the data the enterprise possesses?
All cyber criminals look out for in their target is whether their computers are connected to the Internet or not, period. Once hackers get hold of a computer, then they can use it as a pawn to achieve their goal. A compromised computer can be used as a source of spam messages, as a dumpster for illegal online materials, or to host a phishing website. And since all these crimes will be carried out from the victim’s computer, odds are, security officials won’t be able to trace all such activities back to the real offender.
We already have an AV, so what’s all the fuss about?
Most SMEs, since they are already convinced about their less vulnerability towards cyber attacks, put their entire enterprise security on easily available antivirus software. Here’s a reality check! Malware of today are no where close to what they used to be in the yesteryears. We are talking about malware with innumerous heads, claws and teeth; against which a simple antivirus simply cannot put up a fight.
Reasons Why SMEs Need to take the Whole Hog Approach for Securing their Information Technology?
Probably, the greatest cyber security threat that any enterprise faces is data breach/loss. A single data breach has multiple, and sometimes, irreparable backlashes. Here’s what a data loss/breach of an enterprise may bring with it:
1. Bad Label
When we speak of data that any enterprise keeps or holds, what data are we referring to? The data belongs to the customers the company is dealing with. So a leak of such data means handing over personal and sensitive information of hundreds or thousands of customers into the hands of cyber crooks, which eventually may conclude into a large scale identity thievery. What naturally may follow includes damaging lawsuits, heavy penalties, reputation loss, disgruntled customers, and finally paralysis of business operations.
2. Good for Competitors
Guess what makes competitors of any organization happy, especially an organization that has just started to grow its roots in the market? A potential data loss. When news surfaces that this particular company has a laid-back attitude for protecting its customer’s data, then this only calls for a gala time for its competitors. Where money is involved, maintaining the “trust” coefficient is of immense importance. And security incidents like data loss could be a direct hit to all the foundation a company has laid in order to draw the attention of its potential and existing customers.
3. The Cleanup Cost
The repercussions of a data breach does not end in only disrupting or paralyzing the business. We cannot overlook the mopping part of the story. The cost that is involved in cleaning up the mess, getting the entire system up and running, and starting to build the “trust” coefficient from scratch, is humongous, and sometimes, impossible to cover.
4. Disgruntled Allies
A data breach suffered by an enterprise is not a limiting catastrophe; it spills over to other companies it is connected to and does business with. Even their reputation comes under the axe.
To conclude with an analogy, given the sophistication of today’s malware and their variations, the security perimeter of enterprises, small or big, must begin right from securing the fence, the porch, doors, windows, and even the chimney, if you will. And all such security measures can only be found in reliable, robust, and multi-layered security solutions.
2 Comments
Thank Rajib sir for this helpful blog.
Regards,
Hrushi Sonar.
Thanks….:)