Ransoc – An unusual ransomware that threatens to expose your personal information

Mostly a ransomware encrypts your files and demands money in exchange for a key that can decrypt the data. And the payment is demanded in Bitcoins. Ransoc is different in the way it works and the medium it uses for the payment.
How does Ransoc work?
Once your computer is infected by Ransoc, it gathers your personal information from your Skype and social media profiles and scans your system for Torrent files and other sensitive information. It then displays a ransom note. Interestingly, the ransom note is customized for a particular user and has their social media details including their profile picture. The ransom note threatens the victim with a fake legal proceeding and also that the ‘sensitive’ information found on their computer will be made public if the ransom is not paid.
Now, two important points to note here:
- Ransoc, unlike other ransomware, does not encrypt any files on the infected computer.
- Reportedly, the ransom note is displayed only in a case where the ‘sensitive’ information found by the ransomware includes child pornography or illegally downloaded Torrent media files.
So basically, the creators of this ransomware are targeting the victim’s fear of facing legal complications and losing their reputation instead of their data.
Further, where all ransomware creators use Bitcoin to remain hidden from law enforcement, Ransoc asks its victims to pay via credit card; this kind of payment approach has been unheard of in ransomware attacks till now.
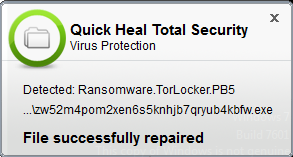
How Quick Heal helps?
Quick Heal’s Virus Protection proactively detects the ransomware as “Ransomware.TorLocker.PB5” and prevents it from performing any activity on your computer.
How to stay safe from ransomware attacks
- Never click on links or download attachments that arrive in emails from unwanted, unknown or unexpected sources.
- Apply all recommended security updates (patches) to your Operating System, and programs like Adobe, Java, web browsers, etc.
- Take regular backups of your files. Remember to disconnect the Internet when you are backing up on a hard drive. Unplug the drive before you go online again.
- Avoid using outdated browser plugins or plugins that you do not use anymore.
- Invest in an antivirus software that comes with several layers of security such as Web Security that blocks infected websites, Email Security that blocks infected emails, Phishing Protection that blocks fake websites, etc.
- Always keep your antivirus software up-to-date to stay safe against new threats.
ACKNOWLEDGEMENT
Subject Matter Expert
– Anita Ladkat (Threat Research and Response Team)


75 Comments
My machine is affected by THOR ransomware in spite of the Quick Hill Total Security in place presently. The Quick Heal telling that those files are ‘Clean’. How the affected files be de-crypted?
Hi Subhendu,
Thank you for writing in. Our support engineers would gladly help you with this. Please call us on our toll-free no. 1800-121-7377 or visit https://bit.ly/QHChat to chat with us online. You can also raise a ticket at https://bit.ly/Askus and we will get back to you at the earliest.
Regards,
it is very very good
This was really helpful to know about Ransoc…
as not purposely but as the advertisements pop ups on any site….i will be careful that time…..and will be having quickheal antivirus only…as i am having now….
THANK YOU
This article is written in studious manner. It shows Quick Heal have well founded research team which works 24×7 to help customer to resolve their issues. This enhances customer’s confidence to buy such a good and updated ptoduct which will safegaurd their system.
I have been using Quick Heal since last 2 year and I dont found any issue yet..I recommend Quick Heal .
I bought this product of 3 years package. First year it worked, after completion of 1 year I am in great trouble. Every second day of update it goes out of security and every second day I have to update. Great trouble is that I have to try atleast 20 to 40 times for update then only it updates (for 1 or 2 days only). Though complained, no one cares. Therefore I suggest do not buy package of 3 years, there is cheating.
This I am talking about my home computer, not this computer. In this computer also I have purchased 3 years package just few months ago, and I fear what will happen after 1 year.
VERY NICE
I am using Quick Heal Internet Security for the past several years. I am fully protected. Internet browsing never posed any problems so far. I am happy with QH antivirus. My best compliments to QH team.
CSC Manisundar
Very helpful.
good choice sequrity
my pc has also affected by ransoc inspite of quickheal
Hi Karan,
Please call us on our toll-free no. 1800-121-7377 or visit https://bit.ly/QHChat to chat with us online. You can also raise a ticket at https://bit.ly/Askus and we will get back to you at the earliest.
Regards,
Ram Amarnani • December 2, 2016 at 10:14 AM
I bought this product of 3 years package. First year it worked, after completion of 1 year I am in great trouble. Every second day of update it goes out of security and every second day I have to update. Great trouble is that I have to try atleast 20 to 40 times for update then only it updates (for 1 or 2 days only). Though complained, no one cares. Therefore I suggest do not buy package of 3 years, there is cheating.
This I am talking about my home computer, not this computer. In this computer also I have purchased 3 years package just few months ago, and I fear what will happen after 1 year
Hi Manish,
Thank you for writing in. Our support engineers would gladly help you with this issue. Please call us on our toll-free no. 1800-121-7377 or visit https://bit.ly/QHChat to chat with us online. You can also raise a ticket at https://bit.ly/Askus and we will get back to you at the earliest.
Regards,
pls don’t public my files keep it safe
It’s very helpful app.
As Your Quick Heal service is taking care, We are fearless . of Virus & Hacking,
1) Its Good
2)Works Faster
3)Its a true ANTIVIRUS
4)Protects Everything of Everyone
5)Never betrays its MasTER
1) RECENLY I WAS GIFTED WITH A QUICK HEAL ANTI VIRUS, BUT UNFORTUNATY MY PC IS VIRUS AFFECTED.
2) PLEASE RECTIFY THE LOOP HOLES, SO THAT I REMAIN TENTION FREE & MY PC REMAIN UNAFFECTED
Hi Dr. ATINDRA,
Thank you for writing in. Our support engineers would gladly help you with this issue. Please call us on our toll-free no. 1800-121-7377 or visit https://bit.ly/QHChat to chat with us online. You can also raise a ticket at https://bit.ly/Askus and we will get back to you at the earliest.
Regards,
The Quick Heal telling that those files are ‘Clean’. How the affected files
Hi Bharat,
Please call us on our toll-free no. 1800-121-7377 or visit https://bit.ly/QHChat to chat with us online. You can also raise a ticket at https://bit.ly/Askus and we will get back to you at the earliest.
Regards,
thank
Hi, whenever I am connecting my pc to internet, a page is opening and showing that update details to quick heal, so this page is opening by quick heal or by any hacker?
Hi Waseem,
Please call us on our toll-free no. 1800-121-7377 or visit https://bit.ly/QHChat to chat with us online. You can also raise a ticket at https://bit.ly/Askus and we will get back to you at the earliest.
Regards,
good quick heal antivirus
Very good activities and good working now
I am using Guardian antivirus for the last two years.it provides the best protection to my computer.I do not hesitate to recommend it for every one.
It is seen thatvirus ransomware affected my PC but the Quick heal cannot cannot clean it.
Hi,
Please call us on our toll-free no. 1800-121-7377 or visit https://bit.ly/QHChat to chat with us online. You can also raise a ticket at https://bit.ly/Askus and we will get back to you at the earliest.
Regards,
We really like this application, on this note, I wish to upgrade quick heal application on my computer.
Hi William,
Thanks for writing in. Please click https://www.quickheal.co.in/upgrade/ to upgrade your product.
Regards,
My product key is FQ0143Y14400628E628A ,Validity stands till 2019 , but unable to update security since 23rd Nov, I tried it 20 to 30 times ,Its a great problem . toll free number 18001217377 nobody receiving for customer support, online chatting also their staffs disconnecting before solving the problem . Should I switch over to other sequrity service .
Hi Sujit,
Thanks for writing in. We have shared your concern with our team; they will get in touch with you to help you out.
Regards,
Device can’t be upgraded
Hi Dheeraj,
Please call us on our toll-free no. 1800-121-7377 or visit https://bit.ly/QHChat to chat with us online. You can also raise a ticket at https://bit.ly/Askus and we will get back to you at the earliest.
Regards,
today my account hake time for11.30AM .12800 maney can be tansfer. sir please help me.
Hi Dipak,
We would advise you to contact your bank and lodge a police complaint.
Regards,
thanks
Help me please
Hi Amit,
Please call us on our toll-free no. 1800-121-7377 or visit https://bit.ly/QHChat to chat with us online. You can also raise a ticket at https://bit.ly/Askus and we will get back to you at the earliest.
Regards,
good
GOOD
My mobile is badly affected due to “Ransom ware.TorLocker.PB5” please solve this problems
Hi Kishan,
Please call us on our toll-free no. 1800-121-7377 or visit https://bit.ly/QHChat to chat with us online. You can also raise a ticket at https://bit.ly/Askus and we will get back to you at the earliest.
Regards,
Dear Sir (s)
On 03-10-2016 I have renewed for one year for the Guardian Net Secure. Reference VINQUICK HEAL/2016100318590000 for rs.499/- The Product Key no is 5Q8288WF1F3770A25510.
Kindly look into this matter and do the needful immediately.
Daily I am getting intimation from you, for the renewal. DO THE NEEDFUL IMMEDIATELY.
Hi,
Thanks for writing in. Our team will get in touch with you soon.
Regards,
I love quick hall
Nice
QUICK HEAL Antivirus pRO
HELPFUL
when ever I start up laptop explorer.exe comes many I had updated quick heal total but still it comes quick heal is not giving proper service
Hi Nayeem,
Please call us on our toll-free no. 1800-121-7377 or visit https://bit.ly/QHChat to chat with us online. You can also raise a ticket at https://bit.ly/Askus and we will get back to you at the earliest.
Regards,
I like
very nice
north of taramandal mandiri main road,patna-800001(bihar)
VERY HELP FULL
This is the best app to remove viruses from our phone
Awesome this app, I like it quick heal
in your pc which oe is virus or quick heal
I don’t know about can this antvirius perform do well but it’s performing satisfy them
One question what can it protect them?
parichha
Hello sir. Thanks for suggestion please suggest me how to stop attometick downlord apps ex game apps atotometick download in my divece plz protect my device lava x11
Hi Mukesh,
Our support engineers can assist you with this. Please call us on our toll-free no. 1800-121-7377 or visit https://bit.ly/QHChat to chat with us online. You can also raise a ticket at https://bit.ly/Askus and we will get back to you at the earliest.
Regards,
Best
Thank you for information and protecting my computer.
Vaidya
THANKS GUADIAN
I AM GLAD MY COMPUTER & LAPTOP ARE “QUICK HEAL” … PROTECTED
good
How can i com to know that my computer is affected by that virus?is it possible to know who want to do this ?Is my device is protected from that virus?
Hi Sasmita,
Thank you for writing in. Our support engineers can help. Please call us on our toll-free no. 1800-121-7377 or visit https://bit.ly/QHChat to chat with us online. You can also raise a ticket at https://bit.ly/Askus and we will get back to you at the earliest.
Regards,
I am interested
How do I know if I my phone is safe? I have got absolutely no idea. Please, keep my phone safe.
Nice ……& service…
I have already visited your office but no one has no solution for this attack and recovery plan instead valuable and super brilliant technical QH staff is well trained to threaten users and blame them how they are responsible for their loss of data and further for which QH have no recovery plan at all,
Even i am punctual in updating the antivirus software and use the legal purchased copy,
But QH is nothing but just dumped trash software which is acquiring my hard-disk space as of now I feel.
And I had to feel this because your engineering team worked so well, hard and made me convinced to believe that it is useless talking and expecting any recovery of my data which is as old as 2009,
And I just want you mention here specially that I am purchasing legal copy of QH from 2009 onwards till now,
And this is the high time for not only me but to all other QH users to really re-think on continuing the use of QH and and move on to any other capable antivirus net protection software.
Thanks and Regards,
Prashant
+91-7028903322