Quick Heal Detects Flash Exploit from China

Quick Heal’s Malware Intelligence reporting system keeps a track of threats that are detected on its customers’ machines. From last quarter’s malware detection stats, we found that there were constant detection alerts for a well-known Adobe flash exploit in India. It is known as CVE-2015-5119. Our analysis of this threat revealed that the attacker had used the Flash exploit POC (Proof of Concept) of Hacking Team that was leaked in July 2015. The attacker had made some small changes to the shellcode of the Hacked Team POC.
Details of the Exploitation
The exploitation begins with the targeted user visiting a compromised website, which contains a malicious advertisement. This advertisement is a malicious IFrame (an HTML document embedded inside another HTML document on a website) redirecting to a compromised URL. This URL loads an Adobe flash file in the victim’s browser that exploits outdated and vulnerable versions of the Adobe flash player plugin installed in the browser.
The Adobe flash file exploits the CVE-2015-5119 vulnerability, and this compromises the browser’s process running on the victim’s machine.
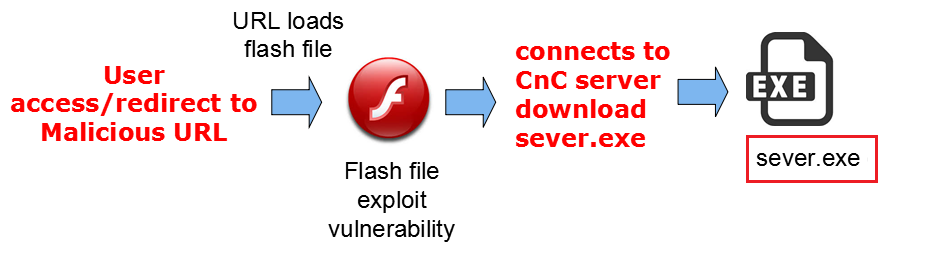
After successful exploitation, the Flash file redirects the execution of the browser process to its custom shellcode. This shellcode is designed to download a sever.exe file from the IP 74.126.180.170 and execute it. The sever.exe file then downloads adware and unwanted software components on the infected machine. The primary intention of the attacker behind carrying out this activity is to earn money; paid out as pay per install.
Detected IP addresses related to this exploit:
- 203.130.60.50
- 61.153.56.60
- 61.160.247.140
- 61.160.224.174
- 222.73.144.176
- 59.46.204.102
How Quick Heal helps
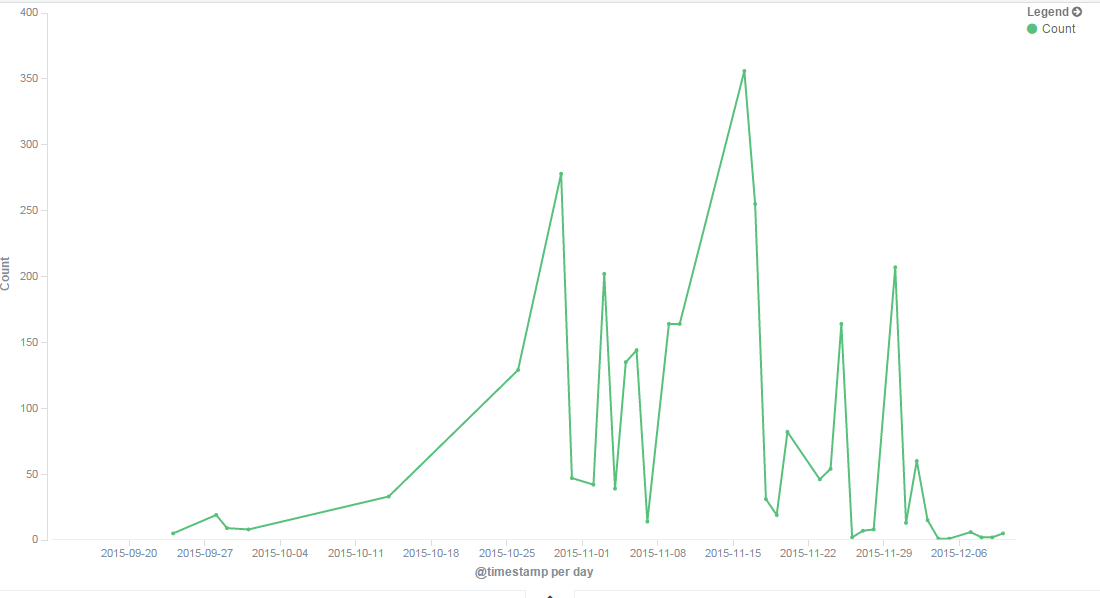
Quick Heal has been detecting this exploit since July 2015; our users are fully protected against it.
Quick Heal detection statistics of the exploit
Acknowledgments:
• Subject Matter Expert: Manish Sardiwal (Vulnerability Analysis & Research Team)
• Quick Heal Threat Research Labs

2 Comments
Hi..
In my Laptop a Security Update for Flash Player shows like this
(Security Update for Internet Explorer Flash Player for Windows 8.1 for x64-based Systems (KB3132372))
Should i update it or not.
Please suggest.
Hi Rahul,
If you have received this update from your system, then do apply it.
Regards,