How smartphone attacks make money at the expense of the victim?
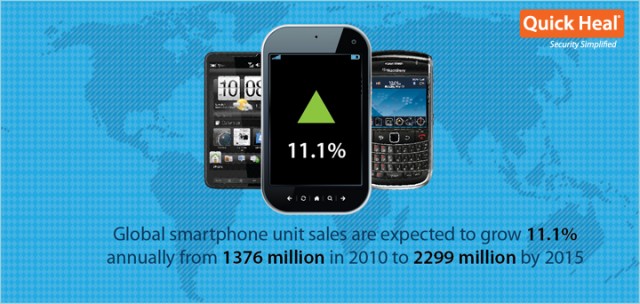
The massive surge in smartphone usage all over the world has allowed scammers to devise several ways to monetize vulnerable devices. For the victim these attack vectors represent a loss of data, time and money. But for the attacker these methods are primarily used to gain monetary benefits.
So how exactly do these attackers make money? Well, they either sell the data that they accumulate to underground buyers who then put it to ill-use. Or they utilize the data they have gained to steal money themselves. Here are the primary methods that attackers adopt to monetize the information that they illegally gain via the different strains of malware and attack vectors.
Earn part revenue through premium-rate numbers
In this scenario, the attacker owns a premium-rate number or is in league with someone who does. He infiltrates a smartphone with malware that automatically sends messages to or calls such numbers. This in turn earns the attacker money and drives up the bill of the unsuspecting phone owner to alarming levels. Some attackers also carry out this highly innovative and organized missed call scam via these premium-rate numbers. For instance, an Opera Mini fake installer is a kind of SMS trojan that sends premium-rate messages. This malware gets installed when someone assumes that he is installing the Opera Mini browser and importantly, such fake installers account for more than 50% of all Android malware.
Earn advertising revenue through free applications
Many application developers offer their products for free and earn their revenue through the advertisements that appear in these apps. Users will be well aware of the free apps and the intrusive ads that they push forward. Scammers can earn money in this manner by pushing a free application to public attention. The revenue that comes in via advertisements is then pocketed by them. Moreover, these ads eat up the Internet bandwidth of users and increase their data consumption as well.
Sell information in international underground markets
The information obtained with the help of malware that steals data can be sold in various underground markets. There are several such rackets that operate under the cloud of the law and they provide high prices for crucial stolen data. This includes, but is not restricted to, contacts, phone numbers, passwords and email addresses. This data is then abused by such buyers for malicious purposes. Droid Deluxe was a notorious spyware that came to light in September 2011 and gained root access to devices and stole email credentials, social network account information and banking login information.
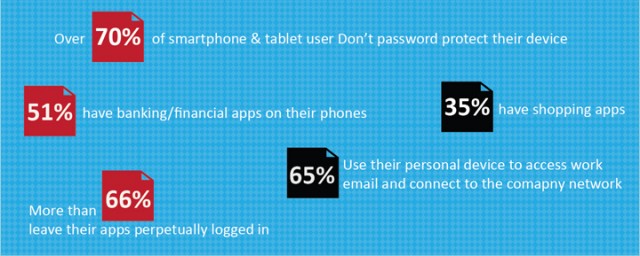
Crucially, there are many people who fail to scrutinize the various permissions that an app demands upon installation. Permissions do not necessarily indicate a malicious app but do point out suspicious ones. People who have granted access to such suspicious apps could suffer from greater privacy concerns as their information can easily be shared with third parties. This information includes user location, the ability to make unsolicited phone calls, access social network accounts and send text messages.
Monetize sensitive phone ID information
Another form of data that can be misused is smartphone IMEI and/or IMSI. These are unique serial numbers that are used to identify handsets and the SIM cards inserted within them. Certain malware strains are designed to steal this information, which can then be sold or misused by the attacker himself. (Note: If you wish to view the IMEI of your phone, type in *#06#)
Misuse credit card data obtained through NFC (Near Field Communication)
NFC enabled smartphones carry sensitive credit card data on them. This data can be unlawfully obtained by attackers with the help of nefarious malware and apps. Credit card information is one of the most sought after items in underground markets so this can be sold for a hefty price. Moreover, the attacker can also misuse the information himself to make fraudulent purchases or transfer money.
Steal money from individuals using their personal financial data
As more people carry out online purchases and access their bank accounts through their smartphones, more financial data is stored on these devices. As a result, cyber crooks follow the masses and launch attacks to get their hands on such information. Personal banking details of individuals can be misused in several established methods and this can lead to identity theft, fraudulent transfer of money to attackers and severe financial loss.
Mobile phone security software is essential today due to the large number of people who own smartphones. Attackers have always devised ways to exploit areas where the masses operate so it was inevitable that smartphones be targeted. Unsurprisingly, the primary motive behind such attacks is money and it is imperative for us to be aware about these attack vectors. However, with high awareness, and the right tools like Quick Heal Mobile Security, you can actively prevent such threats from stealing sensitive information and causing financial loss.


19 Comments
i am very glad and thankful to QUICK HEAL that i can not express in words.You are doing a lot of valuable information to all. May God bless you all as you are saving all from CYBER CRIMINALS.
Hi Ketan,
Thanks for update.Are Iphones better protected against hacking?Which operating system is best.Do you suggest that we should log out from apps like Facebook,Whatsapp & email after each accession from smartphone?
Thanks.
Hi Anant,
Most cases of smartphone malware affect Android phones due to its open-source nature. This downside accompanies the many benefits of open-sourced software. iPhones are also hacked but more malware affects Android. You can log out of the above services after accessing from your smartphone only if you are fine with not receiving the push notifications that they provide in real time.
Regards.
Thanks Rahul for prompt reply
Regards.
Thanks for the info. Many Android apps do request for permissions that are not really required for it to function.
I am a mobile apps developer myself for android and I’m afraid all this is true. Smartphones today are very vulnerable to malware and cyber attacks.
Thanks for your interest in spreading such useful information.
A very Brief Sketch of The Actual Picture ! Hands Off !
Really very useful Info provided by Quick Hill.
Always remember PREVENTION IS BETTER THEN CURE.
Thanks Quick Hill team.
Thanks for the info. Many Android apps do request for permissions that are not really required for it to function.
Very good information and latest update. Keep Going.
“WoW” Thats Really a awesome Information….
Is that Works for other OS also ?
thanks 4 good information…..
thanx rahul.But I have i big problem.I have micromax a45 which has 2.3.6 gingerbread.i had downloaded 1 live wallpaper but now when i uninstall it it comes that application not installed.and i have installed quick heal mobile security and it states 1 ad ware malware something in that live wallpaper.the name of live wallpaper is PLANETS PACK.what to do??
Hi Purve,
Since the uninstallation process isn’t working, you should think about doing a hard reset of your phone. Also, I suppose you downloaded the app from a third-party source and not Google Play? If that is correct then you should always download apps from Google Play in the future. If your problem persists, you can call our support number for assistance – 927-22-33-000.
Regards.
people should not use smartphones
thank u for good information.
Thanks rahul for indepth drive of doomside in Android and smarthphones world today
my quick heel total security not scan properly
Hi Ashish,
kindly visit this link – https://www.quickheal.com/submitticket.asp. You can submit a ticket here and our support team will contact you with a solution.
Regards.