Quick Heal 2013 offers domain and sub-domain control for HTTPS sites
HTTPS protocols are utilized by many websites over the Internet today. This secure layer offers protection against man-in-the-middle attacks and phishing exploits. It also helps a user to detect fake websites that ask for personal information. Traditionally, domains that ask for credit/debit card details and login passwords commonly use this. But now, more and more websites have implemented HTTPS protocols to authenticate themselves to users since it adds a level of certification to them.
Quick Heal 2013 actively allows users to block such websites. Moreover, sub-domains can be controlled as well. The feature can be used by parents to prevent their kids from carrying out financial transactions. It can also be used by employers to control their employees’ browsing activities. For instance, a user can block the Google domain (https://google.com) and this will ensure that all sub-domains of Google (https://mail.google.com, https://news.google.com) are also blocked. Here’s how one can activate this feature:
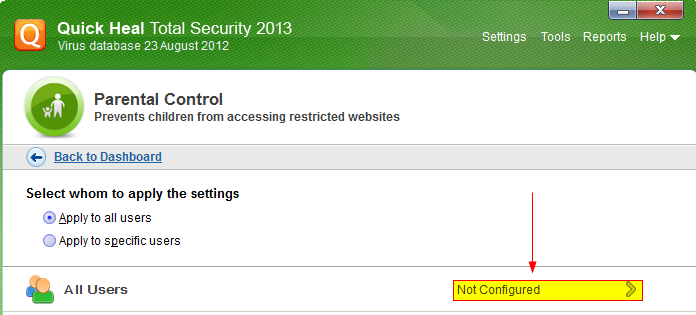
STEP 1 – Open the Quick Heal Dashboard and click on the Parental Control icon.
STEP 2 – Click on the ‘Not Configured’ button.
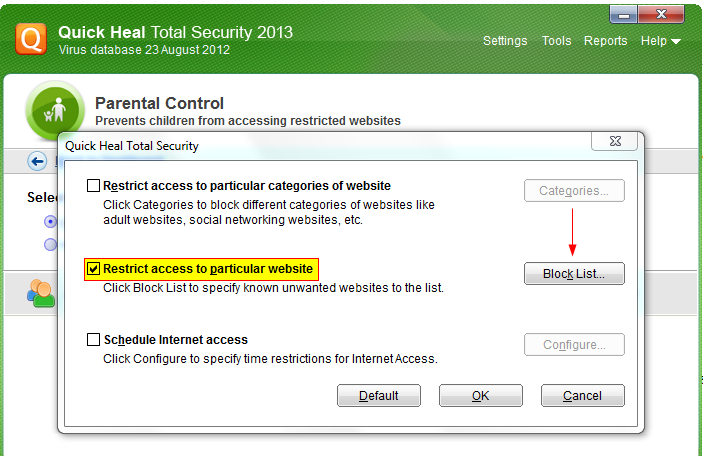
STEP 3 – Click on ‘Restrict access to particular website’ and then click on the ‘Block List’ button to customize settings.
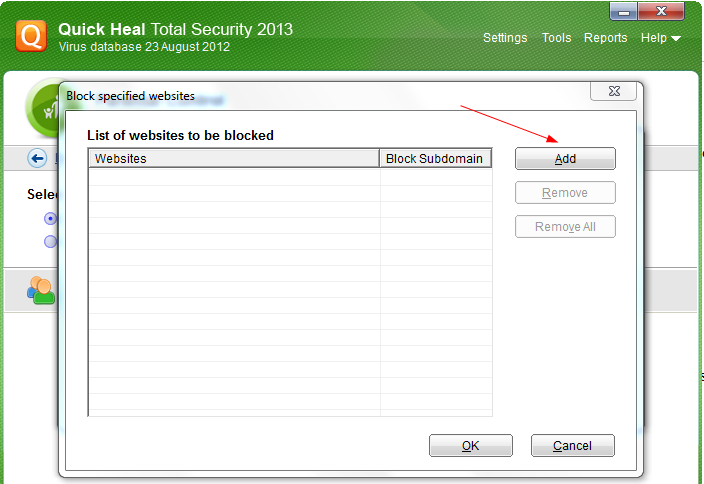
STEP 4 – Click on ‘Add’ to enter a website that you wish to block.
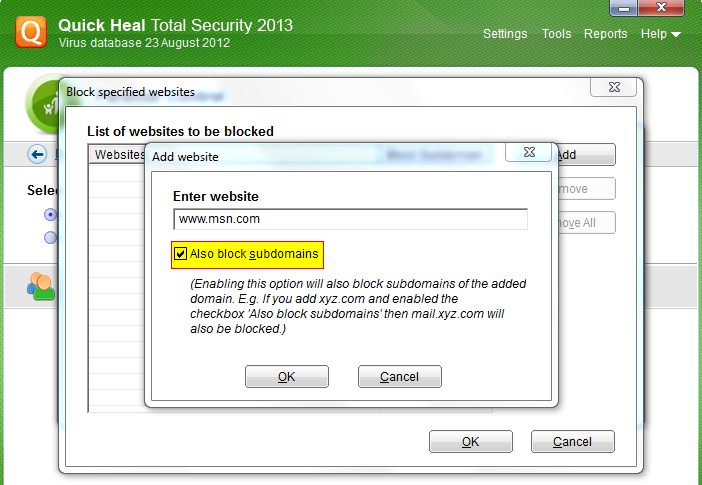
STEP 5 – Enter the website name and check the ‘Also block subdomains’ button. If this box is left unchecked, all the sub-domains of the blocked website will open. Click ‘OK’ and save changes.
Along with Browser Sandboxing this is one of the notable features of Quick Heal 2013. The ability to control sub-domains can be invaluable for parents and employers and we are proud to facilitate this feature. Watch this space for more information about other noteworthy offerings in the latest product line.

38 Comments
I think this feature is very nice but when accessing blocked site it shows notification, this should not be displayed for security reason. If it display other people knows that this site is blocked by Quick Heal Antivirus. So, for security reason this should not be displayed…..
good
Hi,
Referring to the parental control tip given above, say if i block a few websites. The parental control feature does not have a password protection. & person operating the system is aware about the procedure to ubblock the same.
How do you go about in such a scenario
Regrds,
Himesh
Hi Himesh,
You can enable password protection for the same. Click on ‘Settings’, set ‘Password Protection’ to ON and enter a password of your choice. Once activated, no settings can be changed without the password.
Very strong in every soft ware. I like this with Thanks.
WHEN I REGISTERED THIS SOFTWARE IT REQUIRE A PRODUCT KEY. BUT I HAVE NO PRODUCT KEY. FROM WHERE I GET THE PRODUCT KEY AND HOW WILL IT REGISTERED.
PLEASE HELP ME
THANKING YOU
Hi Rahul,
1. The Product Key will be in the user guide or inside the box of Quick Heal. OR
2. If you purchased the product online, the confirmation email will have the Product Key. OR
3. Open the Quick Heal Dashboard, then click on ‘About’ on the left side, then click the ‘License Details’ button to see the Product Key.
Thanks.
thankQ
NICE …..
thanks
world’s no.1 best antivirus
thnkx quickheal products
Hi Alok,
Thanks for your support and loyalty. We appreciate it.
A novice like me want to know the time interval or When of the following :-
i) Full time scan
ii) Memory Scan
iii) Boot time scan
And finally the name of the domain to be blocked or the command to block the non https: domain.
Hi Subhankar,
Memory scan occurs every time Quick Heal automatically updates its virus database. Full-time scan can be carried out once a fortnight. Boot time scan should only be done if there is a heavy infection in the machine that prevents it from starting smoothly.
Thanks.
Thank you Rahul.
Please let me know :-
How the name of the domain to be blocked.
And the command to block the non https: domain.
I am proud to be a quickheal user for the last 6 years. Now my close associates and friends are using the same. This year “Quickheal Internet Security” we are getting at Kolkata Rs.625/-,Rs.1550/- and Rs.2350/- for single, three and five user pack respectively.
My question’s are, i)double/two user pack i.e. for both desktop & laptop for small home office business and ii) Renewal pack should be cheaper online depending upon royalty of the user.
After all we Indians frequently ask “Keta Deti Hai”.
Hi Subhankar,
Please visit the products page for details on the pricing structure – https://www.quickheal.com/products.asp.
If you have further queries, visit this link and our support team will contact you – https://www.quickheal.com/supp_tic.asp.
Thanks.
I Rahul. I am a student so through MSDN dreamspark I would be getting Windows Server 2008 R2. I am geek so I would be installing it as my base OS. I am currently on XP and would like to move to Windows server 2008. I cant buy Windows 7 as ts too costly so would tweak windows server to be used as a workstation OS. My question is will quickheals home use products ie Internet security 2013 and Total security work on server edition? I will be using for home use so can i use my existing key?
Thanks
Hi Bala,
Yes Quick Heal will work on the Windows that you have installed. If you face any issues, visit this link so that our support team can contact you – https://www.quickheal.com/supp_tic.asp.
Thanks.
Ok Thanks Rahul.
Rahul,
In my e-mail box sometimes I got mails don’t know the senders.
And facebook invitation from friends whose account are similar to be known.
How will I know that the above is free from fishing tools or malware or spam .
I do on-line purchase using Credit card.
Hi Subhankar,
You can block such addresses from reaching your inbox. Do not download attachments from such emails as they may contain malware. Regularly scan your machine via Quick Heal to ensure it is fully protected.
Thanks.
Thank you Rahul very much.
Please let me know :-
How the name of the unwanted domain to be blocked.
And the command to block the non https: domain.
Actually i forgot the parent control password how can i retrive it?
Hi Paventhan,
Kindly visit this link – https://www.quickheal.com/supp_tic.asp. You can submit a ticket about your issue and our support team will get back to you with a solution.
Thanks for your patience.
Hi Rahul,
I am using Quick heal total security 2013. When I block some domains and sub-domains through the parental control, it shows notifications for blocking that websites at the time of access.
Can I block that notifications?
Hi Jogesh,
The notifications are necessary to inform the user that those domains have been blocked. Without such notifications a user may feel that there is an issue with Internet connectivity.
Thanks.
Hi Rahul,
Please let me know :-
How the name of the unwanted domain to be blocked.
And the command to block the non https: domain.
Subhankar Ray
world’s no.1 best antivirus
thnkx quickheal products
What if I have forgot the parental control password??
Hi Harshil,
Kindly visit this link – https://www.quickheal.com/supp_tic.asp. You can submit a ticket here about your grievance and our support team will get back to you with a solution.
Regards.
Hi Rahul,
Please reply to my queries of September 10 & 27.
Regards,
Hi Subhankar,
The instructions to do the same are mentioned in the post itself, along with screenshots as well. Kindly refer to the same. If you need detailed help with some feature you can call our support center or visit this link – https://www.quickheal.com/submitticket.asp.
Thanks.
hi rahul,
sir i forgt my quick heal password, i blocked earlier, please help me
Hi Vivek,
Kindly visit this link to submit a ticket about your issue – https://www.quickheal.com/submitticket.asp. Our support team will contact you with a solution.
Regards.
Hi Rahul
I am blocked social websites (like facebook, linkin etc) through quick heal parental control via Categories but the user will open again these websites, please tell me how this possible and tell me the permanent solution
Regards
Pradeep
Hello sir, main janna chahta hu ki iss anti virus me kitne type se kisi individual site ko block kar sakte hai.
Hi Amit,
The “Restrict access to particular website” is the only option in Quick Heal Parental Control feature that allows you to block specific websites. Additionally, you also have the option for blocking particular categories of websites.
Regards,