They come, they hide, and they mess up – Android.Obad and Android.Fakedefender
It looks like malware writers are leaving no stone unturned to target the Android platform. They are exploring every opportunity to do so; one such opportunity recently popped up in the form of two malwares viz. Android.Obad and Android.Fakedefender. Know what these malware are and how they work, from the rest of the post.
Android.Obad and Android.Fakedefender are more sophisticated than the typical malware families. It has been discovered that, these malware can exploit “Device Admin Privileges”, which boost their stealth level after they get installed in a device.
Important Facts about Andriod.Obad
What is it?
- Android.Obad is a Trojan.
- It masks itself as a genuine application.
What does it do?
- It sends SMS to premium-rate numbers, which results in extra cost for user.
- It is capable of downloading other malicious applications, sending them further to Bluetooth-enabled devices, and taking remote commands to perform malicious actions.
How does it gain Device Admin Privileges?
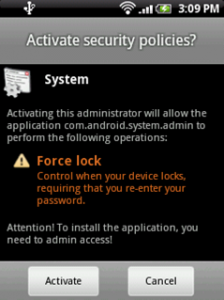
- Once Android.Obad is launched, it keeps asking the user to grant “Device Admin Privileges”. The “Cancel” button is disabled, which leaves the user only with the “Activate” option, as shown in the reference image below:
Some More Facts:
- Once the malware gets access to Device Admin privileges, it dives deeper into the system and hides itself from the device admin list. This action leaves the user with no option to remove the application via Settings.
- Android.Obad makes extensive use of reflection code, which helps it hide its malicious code from the eyes of malware analysts. The strings used and the function names are encrypted with multiple layers using polymorphic techniques.
- Android programs are compiled into DEX (Dalvik Executable) files, which are in turn, zipped into a single APK file on the device. The Android.Obad malware poses challenges for reverse engineering by creating specially crafted DEX (Dalvik Executable) files, for which most of the tools fail to decompile.
Android.Obad takes advantage of the following vulnerabilities, which makes it difficult for analysts to reverse engineer it.
- Modified AndroidManifest.xml: The malware drops some of the components from the manifest file. Because of this, the dynamic analysis environment fails to do an automated analysis of the malware. However, such file is correctly processed by the smartphone’s OS and malware gets executed in the real environment.
- Error in Dex2Jar tool: Dex2jar is a popular tool used for reverse engineering Android malwares. It either fails to decompile or decompiles it incorrectly which makes static analysis difficult.
- Device Admin Privilege: As discussed earlier, Android.Obad takes Device Admin as a special privilege that allows it to hide itself from the Device Admin list.
Important Facts About Andriod.Fakedefender
What is it?
- Andriod.Fakedefender is a Trojan.
- To display itself, it uses icons of popular applications like Facebook and Skype.
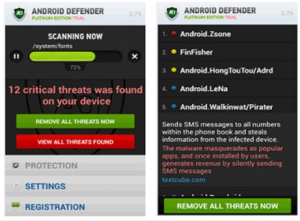
- After it has been installed, it is displayed on the phone as “Android Defender”.
What does it do?
- Once Android.Fakedefender is launched, it keeps asking the user to grant “Device Admin Privileges”. Irrespective of the user’s choice “Device Admin Privileges” are granted.
- The malware starts notifying the user about malware or other security threats that are actually non-existent.
- The malware keeps prompting such messages to scare the user into purchasing apps to remove these threats, thus it is also known as a “scareware”.
- In some cases, the malware may prevent the victim from doing anything else on their phone, until they make a payment.
- It also collects user information like phone number, OS version, device manufacturer, location, etc. and sends it to a remote server.
- The worst part of this malware is its ability to interfere with applications that can warn the user about actual security threats.
Note: Just like Android.Obad, it is also difficult to remove Android.Fakedefender from the device once it has been installed. It changes the device’s settings so that the user is unable to perform a normal factory reset.
We would strongly advice users to be on guard against applications that ask for “Device Admin” privileges.
Definitions of some popular terms used in the post:
- Static Analysis – Static analysis is the analysis of computer software or program that is performed without actually executing it.
- Dynamic Analysis – Analysis performed on executing programs is known as dynamic analysis.
- Reverse engineering – Reverse engineering refers to a process that studies the function and information flow of a piece of software or hardware, in order to determine its technological principles.
- Reflection code – Reflection code refers to the ability of a computer program to examine (see type introspection) and modify the structure and behavior (specifically the values, meta-data, properties, and functions) of an object at runtime.
- APK file – Android application package file (APK) is the file format used to distribute and install application software and middleware onto Google’s Android operating system.
- Automated analysis – Automated Analysis refers to a process that allows malware threat analysts to configure controlled test environments, where they can execute and inspect malware in automated ways.
Blog post acknowledgment – Quick Heal Threat Research and Response Team.
50 Comments
Really very help fully info regarding 2 malware that is Android.Obad and Android.Fakedefender.
Thanks & Regards,
Hrushi Sonar.
HELPFUL, was not aware of these malwares.
thanks for sharing
It is really new for me. Thanks a lot for updating my knowledge about Android.Obad and Android.Fakefender.
Thanks
Anis Balluwala
But in my case the Quick Heal Total Security itself is not able to take either detect the HTC set / if detected then unable to run scanner / if able to run then gets not responding message.
Till date after purchasing the package 4 months earlier – invain.
Pls. guide.
Hi Ganapate,
Kindly contact our support team at 0-927-22-33-000.
You can also raise a query at https://www.quickheal.com/submitticket.asp. Our support team will get back to you to resolve the issue you are facing.
Regards,
thanks for making aware about these two new android malwares.
Really the Android is on the target ……..
Thanks for aware us about malware this info is very helpfull regarding to malware that is Android.Obad and Android.Fakedefender.
Manoj Sahu
But what are the precautions for a non IT/ software person? Pls share info to keep safe too.
Hi Anna,
You can take these precautions:
1. Avoid installing apps that ask for device admin privileges.
2. Always verify apps and their publishers before installing them.
3. Do not keep your phone’s Bluetooth in “visible to all/discoverable” mode when in public places.
4. Ensure that your mobile phone’s security software is always up to date.
Regards,
Hope quick heal has their antidotes. Can we get it?How? When?
thanks
Hi Ranjendra,
Yes, Quick Heal does have antidotes for such malwares. They are in the release process. We will keep you posted.
Regards,
very significant information. a heart felt thanks. but how to get rid of these?
Hi Rupam,
Quick heal detects these malwares and removes them automatically, if the malicious app does not have access to the device admin privileges.
Regards,
This was an excellent article and deserves 10/10.
But what is to be done if : –
1. The phone gets affected by these
2. We have already installed the apps, how to know whether it is malicious or not and if it is malicious what to do next.
3. some extra precautions like not downloading certain apps from certain websites.
Thank you.
Hi Himanshu,
To know whether certain apps are malicious or not, install Quick Heal on your mobile.
If you already have Quick Heal then you need not worry. However, if these malwares have already infected your device and then you install Quick Heal, then it’s not possible to remove them if the device admin privileges are already granted. On the other hand, if admin privileges are not granted then Quick Heal can guide you through the malware removal process.
Here are some precautions you can take:
1. Never install apps that ask for device admin privileges.
2. Always verify apps and their publishers before installing them.
3. Do not keep your phone’s Bluetooth in “visible to all/discoverable” mode when in public places.
4. Ensure that your mobile phone’s security software is always up to date.
Regards,
Thanks for the information =)
Please let me know if you have come up with a defense for this virus / affliction.
You may please charge me for removing and safeguarding from this threat.
TREAT THIS AS MOST URGENT PLEASE
Hello Kesari,
Yes, Quick heal has devised a solution for these malwares, and it’s in the release process. You can take these precautionary measures to keep your devise safe:
1. Never install apps that ask for device admin privileges.
2. Always verify apps and their publishers before installing them.
3. Do not keep your phone’s Bluetooth in “visible to all/discoverable” mode when in public places.
4. Ensure that your mobile phone’s security software is always up to date.
Regards,
How can we install quickheal on android phone.?
Hello Jit,
It’s easy. Simply download Quick Heal Total Security from Google Play. Kindly follow this link.
Regards,
does the quick heal total security version for android have the tenets to counter them.if not how can we keep our mobiles safe?
Hi Arup,
Yes, Quick heal has devised a solution for these malwares and it’s in the release process.
To add, you can follow these security measures to keep your mobile device safe from such malwares:
1. Never install apps that ask for device admin privileges.
2. Always verify apps and their publishers before installing them.
3. Do not keep your phone’s Bluetooth in “visible to all/discoverable” mode when in public places.
4. Ensure that your mobile phone’s security software is always up to date.
Regards,
This is serious and thanks Mr. Mane to bring it upto notice.
Malwares cvause havoc with systems now with devices lie mobile.s
They are unproductived, time money wasters. causes potential breakdowsn.
Increases stress lveles, loss of business.
Pls take due notice to avoid downsloading too many things like games, apps, theemes from untrusted sources.
Sb
Thanks for the info. But what about the remedy if someone is hit by this malwares. How do you remove it or which tools are able to successfully remove it or is it necessary to wipe clean the phone?
Hello Mr. Sajid,
If a user has preinstalled Quick Heal then they need not worry. However, if these malwares have already infected their device and then they install Quick Heal, then it’s not possible to remove them if the device admin privileges are already granted.
On the other hand, if admin privileges are not granted then Quick Heal can guide the user through the malware removal process.
Regards,
Thanks for your valued information. Plz. keep it up to make our tech world malware free and alert to get rid off them.
Thanks once again
Thank You Sir. Please continue sharing of such type of information to secure our andorid devices.
Thanks, using android phone, will be helpful.
Does Quickheal can remove this viruses?
Hi Sharad,
Quick heal detects these malwares and removes them automatically, if the malicious app does not have access to the device admin privileges.
Regards,
Thanks , Keep updating.
how to identify if my android device is affected with this malware? and how to remove it?
Hi Parin,
Install Quick Heal on your device. That will help you identify them.
Quick heal detects these malwares and removes them automatically, if the malicious app does not have access to the device admin privileges.
Regards,
thankyou for information thankyou very much
thankyou for informating
I bought Quick heal total security a couple of years back for three and half years. I am surprised to see that people are so lazy and idle not to improve anything! I have been complaining since 2010 to add android phones in mobile security facility.
I really hate Quick Heal now and suggest everyone never to buy it. QuickHeal has time to design a new android app for android apps to earn 50/100 Rs. but they are so mean not to keep their promise to provide one of the features in their total security software.
We are really ashamed of such people who belittle the fame and growth of our nation everyway!!
Hello Dr. Raval,
Quick Heal security solutions not only cover desktops but also mobile platforms such as Android and Blackberry. You can avail Quick Heal mobile security for Android or BlackBerry, or Quick Heal Total Security for Android phones, which offer additional benefits. For more details on these products you can follow this link.
Furthermore, Quick Heal also offers PC2Mobile scan service to a wide range of mobile phones. Visit this link to know more about it.
If PC2Mobile Scan does not support your device, you can raise a request for the same. Kindly follow this link.
Regards,
OK, understood the problem… what is the solution.
How to avoid installation of these malwares.
Thanx
Hi Mr/Ms Jain,
Here are some steps that can help reduce the risk of installing such malwares:
1. Never install apps that ask for device admin privileges.
2. Always verify apps and their publishers before installing them.
3. Do not keep your phone’s Bluetooth in “visible to all/discoverable” mode when in public places.
4. Ensure that your mobile phone’s security software is always up to date.
Regards,
so what!you are with us,thank you Quick Heal thank you.
Thanx 4 sharing…
I am using Quick Heal Total Security for Android Smartphone in my Lenovo smartfone for the past one month, does it automatically prevent the malwares from entering the phone, pls advise if it need to be done manually.
Hi Harish,
Yes, if Quick Heal is already installed on the mobile, then it detects these malwares and can guide the user through the removal process.
Regards,
Very Helpful info….. But one question arises in my mind that if these apps present themselves in the form of Facebook or Skype apps then how do we recognize them… Please suggest.
Hi Supradip,
Apps such as Facebook and Skype do not request for device admin privileges. So, if such apps are asking for the same, then a user can recognize them as malicious apps.
Regards,
Thanks a lot…….
RAJA
ASSAM, GUWAHATI, INDIA
awareness makes more alert to go through handling such application with caution while downloading either or permitting to it for.
Thanks for making aware of it.
Dr. Chetan Batavia
Gujarat.
can quickheal be a safeguard against these malwares in an andrioid phone?
Hi Sandeep,
Yes, Quick Heal can protect your Android phone against such malwares.
Regards,
ya it is helpful for me thanks Quick Heal
WHEN WE CAN SE QUICK HEAL 2014 ALSO CAN U SHARE SOME NEW IN 2014