The State of Android Malware in 2014
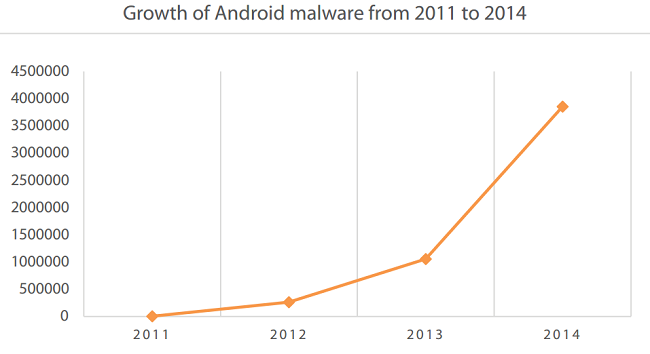
In the year 2014, Android usage and malware saw an exponential rise vis-à-vis preceding years. Quick Heal Labs detected close to 3 million malware samples throughout the year and several new attack vectors and techniques were propagated by malware authors throughout the globe. Some malicious apps were even spotted in the Google Play store and fake games, apps and antivirus applications were regularly used to dupe unsuspecting users. Common Windows based attack techniques such as adware and ransomware became popular over Android as well, and this highlighted a growing trend that malware is becoming device agnostic.
Since 2011, the number of Android malware samples detected by Quick Heal has risen a staggering 304 times. In 2014, the Quick Heal Threat Research Labs discovered 536 new families in the category of Android adware, malware and potentially unwanted programs (PUPs). A further 616 new variants afflicting the Android platform were also detected.
Top 10 Android malware variants 2014
Out of all the samples that were discovered in 2014, here are the top 10 variants that Quick Heal Labs detected.
- Android.Viser.A
- Android.Mobclick.A
- Android.Gedma.A
- Android.Coogos.Ad388
- Android.Agent.DL
- Android.Smsreg.W
- Android.Domob.A
- Android.Invis.A
- Android.SeaWeth.D
- Android.SecApk.A
Users who have Quick Heal installed on their Android smartphones were secured against these threats. In order to combat these growing variants of Android malware and other samples, you can also download Quick Heal Mobile Security for free. Read more here.
Notable highlights of Android malware from 2014
Here are several key highlights that were discovered with regards to Android malware in 2014.
First fake paid application on Google Play
The first fake paid application was discovered on Google Play. This app was called Android.VirusShield.A and claimed to be an antivirus app. In reality, it stole and broadcasted confidential data from Android smartphones.
First Remote Access Toolkit (RAT) on Google Play
The very first RAT was discovered over Google Play and this went by the name of Android.Dingwe.A. It had the capability to remotely control the access and status of a device once it entered.

Ransomware afflicted Android devices worldwide
Ransomware locks up a device and demands payment in order to grant access to the device owner again. This has been a popular attack vector over Windows for many years, but now ransomware has reached Android users as well. Top ransomware samples that were detected in 2014 were Android.Koler.A and Android.Simplocker.A.
First Worm spreads through SMS
A worm called Android.Selfmite.B actively spread through Android devices via text messages. The worm cleverly disguised itself within infected machines and propagated itself to a further 20 contacts from each infected device.
First boot-kit spreads on Android
Android.Oldboot was a first of its kind virus found on Android in 2014. It cleverly modified the device partition within Android devices and modified the boot script as well to gain unsolicited access to the content of infected Android devices.
For more such insights and analysis into the state of Android malware 2014, have a look at the Annual Threat Report created by the Quick Heal Threat Research Labs. This report contains a lot more information about Android malware samples detected, future trends and predictions and several more facts and figures that all Android smartphone users should be in the know of. Stay tuned for more such information on all our channels.
7 Comments
under “important malware information ” on your website, it is mentioned that keyloggers, network administration tool, remote administration tools and certain spyware can be intentionally installed or can be used for illegal purpose as well. Does quickheal for android detect these threats in both cases?
Plz check any virous in my mobile and solve the problem
Hi Saiful,
If you have Quick Heal installed in your phone, you can carry out a system scan from the Settings of the app. Alternatively, you can also use the PC2Mobile Scan feature that is available with Quick Heal Total Security. Via this feature, you can plug in your phone to your PC and then scan the phone through the Quick Heal dashboard.
Regards.
Good
One viruses not remove.
Help me.
Hi Yashdeep,
We recommend that you contact our technical support team for assistance. They will be able to resolve this issue for you immediately. You can reach them in the following two ways:
1. You can call them on 0-927-22-33-000.
2. You can submit a ticket by visiting this link – https://www.quickheal.co.in/submitticket.
Best regards.
344235 52190Howdy! I just wish to give a huge thumbs up for the fantastic info you might have here on this post. I will probably be coming back to your weblog for much more soon. 958554