Alert! A Fake Flash Player Website is Spreading Locky Ransomware

The Locky ransomware, like all other ransomware, encrypts user data and demands a hefty ransom in exchange for the key that decrypts the data.
A variant of this ransomware called ‘thor’ was recently found being distributed via a fake ‘Flash Player Update’ downloading website that goes by the name ‘fleshupdate.com’. The distribution of unwanted software and PUAs through such fake updates has been reported on several other occasions earlier as well. This distribution technique only goes to show how attackers are trying hard to maximize their target area. If you notice, the word ‘flash’ has been wrongly spelled in the domain name – ‘fleshupdate.com’.
What happens when a user visits this fake website?
When a user lands on this website, they are greeted by a fake web page stating ‘Your Flash Player may be out of date’. To a normal, unsuspecting user, this web page will look exactly like the real Adobe site.
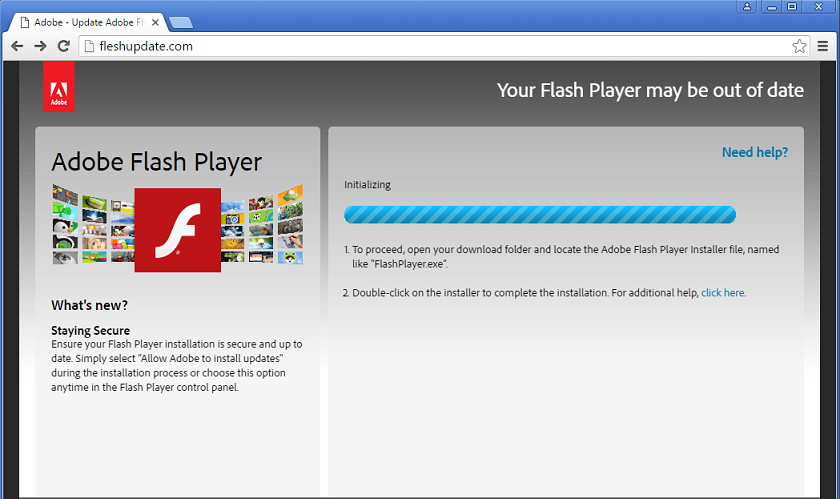
Fig 1. Fake Flash Player web page
Almost instantly, the fake page gets automatically redirected to a malicious URL (highlighted below), which then begins downloading the Locky ransomware variant on the user’s computer.
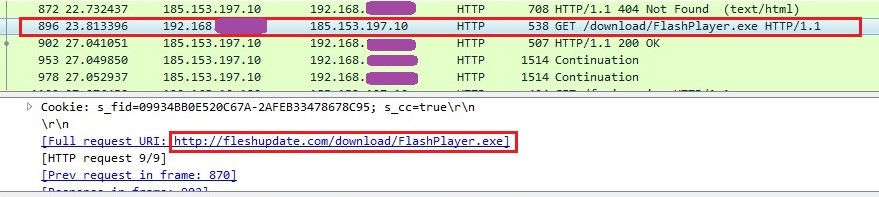 Fig 2. Malicious Locky executable download URL
Fig 2. Malicious Locky executable download URL
The malicious executable file is downloaded with the name ‘FlashPlayer.exe’ and carries the icon of the genuine Flash Player to fool the user.
![]()
Fig 3. Malicious executable file with the Flash Player icon
Noticing the harmless-looking icon, when the unsuspecting user considers this file as a genuine one and runs it, the ransomware starts scanning the infected computer for file types that it supports and encrypts them. The malware adds the ‘.thor’ extension to the encrypted files and this is followed by the ransom note.
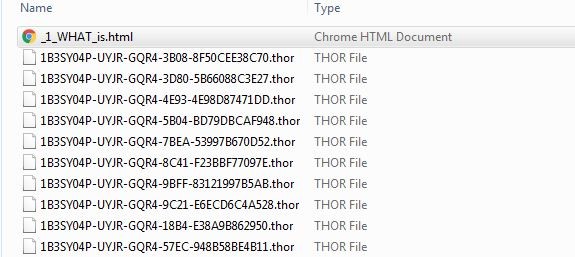
Fig 4. Encrypted files with ‘.thor’ extension
How Quick Heal helps?
Quick Heal’s inbuilt Browser Protection proactively blocks access to malicious URLs/websites that can trigger the download of ransomware and other malware on your computer; in this case, it blocked the URL ‘fleshupdate.com/dow7878nload/flashplayer.exe’
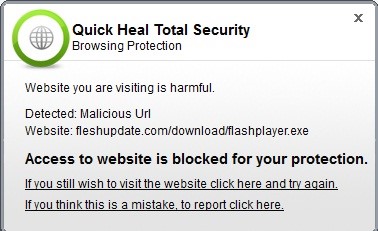 Fig 5. Quick Heal Browsing Protection Alert
Fig 5. Quick Heal Browsing Protection Alert
Quick Heal proactively detects the malicious component as ‘TrojanRansom.Locky’.

Fig 6. Quick Heal Virus Protection Alert
How to stay safe against ransomware attacks
- Before accessing any website, always verify its URL; look for spelling errors and junk characters.
- Never click on links or download attachments that arrive in emails from unwanted, unknown or unexpected sources.
- Apply all recommended security updates (patches) to your Operating System, and programs like Adobe, Java, web browsers, etc.
- Take regular backups of your files. Remember to disconnect the Internet when you are backing up on a hard drive. Unplug the drive before you go online again.
- Avoid using outdated browser plugins or plugins that you do not use anymore.
- Invest in an antivirus software that comes with several layers of security such as Web Security that blocks infected websites, Email Security that blocks infected emails, Phishing Protection that blocks fake and phishing websites, etc.
- Always keep your antivirus software up-to-date to stay safe against new threats.
ACKNOWLEDGEMENT
Subject Matter Expert –
Prashil Moon (Threat Research and Response Team)


3 Comments
Thanks. Does Quick Heal Antivirus Pro detect it?
Also please improve your Phishing protection on QHIS & QHTS. There are various Phishing URL on PhishingTank [ https://www.phishtank.com/ ] but QHTS does not detect as Phishing. Firefox browse detect as Deceptive Site or Reported Unwanted Software Page. Please check it. Thanks.
Locky Ransomware affected but using microsoft security essential scan affected files in extension of AESIR files. If i install quick heal any possibility to retrieve the data. Pl help me.
Hi,
Thank you for writing in. Our support engineers would gladly help you with this. Please call us on our toll-free no. 1800-121-7377 or visit https://bit.ly/QHChat to chat with us online. You can also raise a ticket at https://bit.ly/Askus and we will get back to you at the earliest.
Regards,